Managing business data is no longer a simple matter of storage. For Michigan small and medium-sized businesses, especially those in regulated fields like healthcare, education, or manufacturing, a well-defined data retention policy is a critical component of operational resilience, cybersecurity, and legal defense. Failure to manage the data lifecycle effectively creates significant risks, from compliance penalties and inflated storage costs to severe security vulnerabilities. An unstructured approach-keeping everything forever-is not a strategy; it is a liability waiting to happen.
This guide outlines 10 actionable data retention policy best practices designed to help you build a robust, defensible, and efficient framework. We will move beyond high-level theory and provide a clear roadmap for creating, implementing, and maintaining a policy that not only meets legal requirements but also strengthens your overall data governance posture. Each practice is broken down into specific steps you can take to protect your organization’s information, whether it’s patient data under HIPAA, student records, or sensitive government documents.
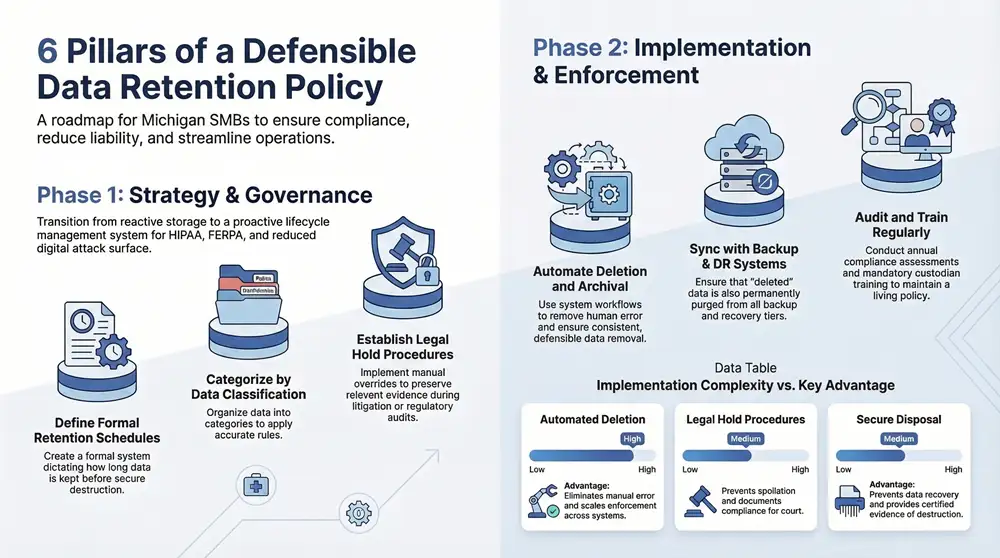
A proactive strategy is fundamental to turning a compliance necessity into a strategic advantage. It reduces your organization’s attack surface, streamlines eDiscovery processes, and ensures you are prepared for audits and legal inquiries. To move beyond reactive compliance, a deep understanding of regulatory compliance risk management is essential for developing truly proactive data retention policies. This list provides the foundational steps to get there, helping you transform your data management from a cost center into a streamlined, secure, and value-driven operation.
1. Define Clear Retention Schedules Based on Business Function and Compliance Requirements
A foundational component of any effective data retention policy is a clearly defined retention schedule. This schedule is a formal document or system that dictates how long specific types of data must be kept and when they should be securely destroyed. The core principle is to retain data only as long as it is necessary for legal, regulatory, or business purposes, thereby minimizing risk, reducing storage costs, and improving data management efficiency. For Michigan businesses, this involves navigating a complex web of federal laws like HIPAA and state-specific regulations.
Without a formal schedule, organizations often fall into one of two traps: keeping everything indefinitely, which increases liability and storage costs, or deleting data prematurely, which can lead to severe compliance penalties. A well-structured schedule ensures a consistent, defensible process for data disposition that aligns with your operational needs and legal obligations.
Why This Is a Core Best Practice
Implementing clear retention schedules is crucial because it provides the structure needed to manage the data lifecycle systematically. It directly addresses the “data minimization” principle found in many privacy laws, ensuring you only hold onto what is absolutely necessary. This practice is not just about compliance; it’s a strategic business decision that enhances security by reducing the amount of data exposed to potential breaches. A clear schedule simplifies legal discovery processes and demonstrates due diligence to regulators.
How to Implement Retention Schedules
Follow these actionable steps to create and maintain your data retention schedule:
- Conduct a Data Inventory: Begin by identifying and categorizing all the data your organization creates, collects, and stores. Classify data based on its function, such as financial records, employee files, customer information, or patient health records.
- Identify Legal Requirements: Work with legal counsel to map out all applicable federal, state, and industry-specific regulations. For example, a Michigan healthcare provider must retain HIPAA-related records for a minimum of six years, while a K-12 school must adhere to FERPA guidelines for student records. Understanding these obligations is critical. For more information, you can learn more about navigating cybersecurity regulations on kraftbusiness.com.
- Create a Retention Matrix: Develop a comprehensive matrix or table that lists each data category, the specific retention period, the legal or business justification for that period, and the designated data steward responsible for its management.
- Automate and Communicate: Integrate your retention schedule into your Document Management System (DMS) or other data platforms to automate the process. Clearly communicate the policy and schedule to all employees to ensure organization-wide adherence.
- Review and Update Annually: Regulations and business needs change. Schedule an annual review of your retention schedule to ensure it remains current and effective.
2. Implement Automated Data Deletion and Archival Processes
Once a clear retention schedule is in place, the next critical step is to automate the enforcement of those rules. Automated data deletion and archival processes involve using software and system workflows to systematically manage data at the end of its lifecycle without manual intervention. This approach ensures that data is consistently and defensibly deleted, archived to lower-cost storage, or anonymized once its predetermined retention period expires, drastically reducing the risk of human error.
Manual deletion is often inconsistent and difficult to audit, leaving sensitive data on systems far longer than necessary. Automation transforms the data retention policy from a document on a shelf into an active, operational control that works across all your systems, from primary servers to cloud backups. This systematic process provides an auditable trail, proving that your organization is compliant with its own policies and with regulations like HIPAA.
Why This Is a Core Best Practice
Automating data disposition is fundamental to modern data retention policy best practices because it ensures reliable and uniform policy enforcement. It eliminates the “what if we need it someday?” mentality that leads to data hoarding and increased risk. For a Michigan manufacturing firm, this could mean auto-archiving historical production data to tiered storage after five years. For a school district, it could mean the scheduled deletion of temporary student files after graduation, ensuring compliance with FERPA. Automation provides consistency, reduces labor costs, and creates a defensible audit trail of every action taken.
How to Implement Automation
Follow these actionable steps to automate your deletion and archival workflows:
- Integrate with Your DMS: Leverage the capabilities within your Document Management System (DMS) or information governance platform. Configure these systems to apply the retention rules you created in your schedule to specific data classifications.
- Start with Low-Risk Data: Begin your automation journey by targeting lower-risk data categories, such as expired marketing materials or old departmental memos. This allows your team to test and refine workflows in a controlled environment before moving on to more sensitive information.
- Implement Comprehensive Logging: Before enabling automated deletion, ensure that robust logging is active. Every action, whether an archive or a deletion, must be recorded in an immutable log. This provides the auditable proof needed for compliance and internal governance.
- Build in Legal Hold Overrides: Your automation must have a built-in mechanism to recognize and respect legal holds. Create flags or triggers that can be applied to data subject to litigation, ensuring these workflows are immediately paused for that specific data set.
- Test and Verify: Regularly test your automated processes. This includes verifying that backups of deleted data are also properly purged according to the policy and testing disaster recovery procedures to ensure archived data remains accessible and intact.
3. Establish Legal Hold Procedures for Litigation, Investigations, and Regulatory Inquiries
A critical exception to any standard data retention schedule is the legal hold. Also known as a litigation hold, this is a formal process that overrides normal data destruction protocols to preserve all forms of relevant information when an organization reasonably anticipates litigation, a government investigation, or a regulatory audit. Failing to implement a legal hold can result in severe penalties for spoliation, which is the intentional or negligent destruction of evidence.
This process ensures that crucial data is protected from deletion, whether manual or automated, for the duration of the legal matter. For a Michigan manufacturing firm facing a product liability suit, this could mean preserving quality control documentation and engineering emails. Similarly, a K-12 school district must preserve all relevant records during a Title IX investigation. A proper legal hold is a cornerstone of defensible data retention policy best practices.
Why This Is a Core Best Practice
Implementing a formal legal hold procedure is non-negotiable for risk management. It provides a structured, documented, and defensible response to legal obligations, demonstrating that your organization has taken deliberate steps to prevent the loss of potential evidence. This systematic approach protects the company from accusations of spoliation, which can lead to court sanctions, adverse inference instructions to a jury, and significant financial penalties. It also ensures that legal and IT teams can work together efficiently to identify, preserve, and manage data without disrupting business operations.
How to Implement Legal Hold Procedures
Follow these actionable steps to build a robust legal hold process:
- Define Trigger Events: Work with legal counsel to clearly identify what events will trigger a legal hold. This could include receiving a subpoena, a demand letter from an attorney, a formal notice of a lawsuit, or even the credible threat of litigation.
- Create a Legal Hold Notice Template: Develop a standardized template for notifying relevant employees (custodians) of their obligation to preserve data. The notice should clearly define the scope of the hold, the types of information to be preserved, and the consequences of non-compliance.
- Establish a Centralized Tracking System: Maintain a centralized registry or log of all active legal holds. This log should document the case or matter name, the date the hold was issued, a list of all custodians, and the status of the hold.
- Train Key Personnel: Ensure that IT staff, records managers, and department heads are trained to recognize trigger events and understand their roles and responsibilities once a legal hold is initiated. They must know how to suspend automated deletion routines for specific data sets.
- Document Everything: Meticulously document every step of the process, from the initial trigger event to the final release of the hold. This includes copies of all notices sent to custodians and their acknowledgments of receipt.
4. Conduct Regular Data Audits and Retention Compliance Assessments
A data retention policy is only as effective as its implementation. Regular data audits and compliance assessments are the mechanisms that verify your policy is working as intended. This process involves systematically reviewing and validating that data is being retained, archived, or deleted according to your established schedules and that the underlying processes are functioning correctly. For a Michigan manufacturing firm, this could mean auditing quality and safety documentation to ensure compliance with industry standards.
Without periodic audits, policies can become mere documents, leading to “data hoarding” or accidental deletion. An audit acts as a critical feedback loop, identifying gaps, unauthorized data accumulation, and areas where governance has weakened. It provides tangible evidence that your organization is actively managing its data lifecycle, which is crucial for demonstrating due diligence to regulators and stakeholders.
Why This Is a Core Best practice
Auditing is fundamental because it transforms your data retention policy from a static rulebook into a dynamic, living process. It is a proactive measure that uncovers compliance risks before they escalate into costly penalties or data breaches. By systematically checking your practices against your policy, you can identify and remediate issues like inconsistent application of retention rules across departments or technical failures in automated deletion workflows. This practice ensures accountability and continuously refines your data management strategy, making it one of the most important data retention policy best practices.
How to Implement Regular Audits
Follow these actionable steps to establish a robust data audit program:
- Establish an Audit Schedule: Define a regular cadence for audits, such as annually or semi-annually. Consider scheduling them during periods of lower operational demand to minimize disruption.
- Form a Cross-Functional Team: Assemble an audit team that includes representatives from IT, legal, compliance, and key business units. This multidisciplinary approach ensures a comprehensive review that considers technical, legal, and operational perspectives.
- Define Audit Scope and Methodology: Clearly document what systems, data types, and departments will be audited. Outline the methodology, including how data samples will be selected and what criteria will be used to assess compliance.
- Utilize Automation: Leverage automated tools and scripts to scan systems and repositories. These tools can efficiently analyze vast amounts of data to identify files that have exceeded their retention period or are stored improperly, reducing the burden of manual sampling.
- Document and Report Findings: Create a detailed report of the audit’s findings, highlighting areas of non-compliance, potential risks, and root causes. Present these findings to executive leadership along with a clear risk assessment.
- Develop and Track a Remediation Plan: For each finding, create a prioritized remediation plan with specific actions, assigned owners, and realistic timelines. Track progress against this plan and conduct follow-up audits to verify that the corrective actions have been effective.
5. Integrate Data Retention Policies with Backup and Disaster Recovery Systems
A robust data retention policy is incomplete if it only addresses production data. It must extend to all copies of that data, including those in backup and disaster recovery (DR) systems. This best practice involves synchronizing your retention schedules with your backup and DR processes to ensure that when data reaches its end-of-life, it is permanently and verifiably removed from all storage tiers, preventing accidental restoration of information that should have been purged.
Without this integration, organizations create a critical compliance gap. For instance, a Michigan healthcare provider might delete a patient record from their live system after the required six-year period, but that same record could persist for years in monthly or yearly backup tapes. This oversight not only increases storage costs but also exposes the organization to legal risks during eDiscovery and potential non-compliance penalties if that data is ever breached or improperly restored.
Why This Is a Core Best Practice
Integrating retention policies with backup and DR systems is crucial for maintaining a consistent and defensible data disposition strategy. It ensures that your data deletion practices are thorough and that you aren’t unknowingly holding onto liability in your archives. This alignment is fundamental to true data minimization, reducing the attack surface for cyber threats and simplifying compliance audits. It proves to regulators and legal teams that your organization has end-to-end control over its data lifecycle.
How to Implement This Integration
Follow these actionable steps to align your retention, backup, and DR processes:
- Map the Complete Data Lifecycle: Document the flow of data from its creation in production systems through its journey into short-term backups, long-term archives, and DR copies. Identify every location a piece of data might exist.
- Align Backup Schedules with Retention Policies: Create backup job retention settings that mirror your data retention schedule. For example, if employee records must be kept for seven years, ensure your backup system does not retain copies of those records beyond that timeframe. To dive deeper, you can explore best practices for data backup and recovery on kraftbusiness.com.
- Establish Clear Ownership: Assign responsibility for managing and purging data at each storage tier. The IT team managing backups must be fully aware of and accountable for enforcing the data retention policy within their systems.
- Test Deletion and Recovery Procedures: Periodically test your processes by attempting to recover data that should have been permanently deleted according to your policy. This validates that your integrated system is working correctly.
- Update DR Plans: Ensure your disaster recovery procedures include steps to honor retention policies. The DR plan should not inadvertently restore data that was intentionally and permanently deleted from production systems prior to the disaster event.
6. Document Retention Policy Development and Custodian Training
A data retention policy is only effective if it is formally documented and consistently followed. This best practice involves creating a comprehensive document that outlines every facet of the policy-from its purpose and scope to its specific implementation procedures-and establishing a robust training program for the employees, or data custodians, who manage the data. Without clear documentation and training, even the most well-designed policies can fail due to inconsistent application, leading to compliance gaps and increased risk.
The goal is to create a single source of truth that is defensible to auditors and regulators while empowering your team to manage the data lifecycle correctly. For Michigan organizations in regulated sectors like healthcare or education, documenting the rationale for each retention period and proving that staff are trained on these rules is a critical component of demonstrating due diligence. This formal approach transforms an abstract policy into an operational reality.
Why This Is a Core Best Practice
Formal documentation and training are essential because they ensure accountability and consistency across the organization. A detailed policy document provides a clear, official reference that eliminates ambiguity and supports uniform implementation. Training ensures that data custodians understand their specific responsibilities and the legal and business context behind them. This combination is fundamental to building a culture of data compliance and is one of the key data retention policy best practices for mitigating human error, which remains a primary cause of data-related incidents.
How to Implement Policy Documentation and Training
Follow these actionable steps to document your policy and train your team:
- Develop a Comprehensive Policy Document: Start with a clear policy statement defining the purpose, scope, and responsibilities. Include the detailed data classification scheme and the retention schedule, citing the specific legal or business justification for each retention period. Appendices can detail procedures for specific systems.
- Establish a Review and Approval Process: The policy document should be a living document. Institute a formal process for an annual review and update, with version control and a clear approval chain involving legal, IT, and business leadership.
- Integrate Training into Onboarding: Make data retention policy training a mandatory part of the onboarding process for all new hires. This sets clear expectations from day one and ensures immediate awareness of data handling responsibilities.
- Conduct Annual Refresher Training: Schedule mandatory annual training for all relevant employees to cover policy updates, address common questions, and reinforce key principles. Document who attended and when the training was completed. For example, a Michigan school district could train administrators on new FERPA guidelines annually.
- Assign and Empower Data Custodians: Formally assign data custodians for different data categories and clearly define their roles. Where appropriate, tie adherence to the data retention policy to employee performance reviews to underscore its importance.
7. Address Data Classification and Categorization to Enable Accurate Retention Decisions
Before you can apply retention schedules effectively, you must first understand what kind of data you have. Data classification is the process of organizing data into categories based on its sensitivity, business function, and regulatory requirements. This crucial step enables you to apply the correct retention rules and security controls to the right information, forming a core component of your data retention policy best practices.
Without proper classification, organizations treat all data as if it has the same value and risk level. This leads to either over-retaining low-value data or, more dangerously, failing to protect and retain critical information according to legal standards. For instance, a Michigan manufacturing firm needs to treat its proprietary engineering designs differently than its public marketing materials, applying stricter access controls and longer retention periods to the former.
Why This Is a Core Best Practice
Data classification provides the clarity needed to enforce your retention policy accurately and consistently. It allows you to prioritize security resources on your most sensitive assets and streamline the disposal of non-critical information. By categorizing data, you can automate retention rules more effectively, reduce the risk of human error, and demonstrate a structured, intentional approach to data governance to auditors and regulators. It connects the “what” (the data) with the “how long” (the retention schedule).
How to Implement Data Classification
Follow these actionable steps to create a functional data classification system:
- Establish a Simple Taxonomy: Start with a few broad categories that are easy for employees to understand, such as Public, Internal, Confidential, and Restricted. Define clear criteria for what belongs in each category.
- Identify and Categorize Key Data: Focus on critical business and regulated data first. A healthcare provider in Michigan might classify patient health records (PHI) as “Restricted,” employee payroll information as “Confidential,” and internal training documents as “Internal.”
- Integrate Classification into Workflows: Embed classification into your daily operations. This can be done by requiring users to tag documents upon creation, using automated tools that classify data based on keywords or location, or setting default classifications for specific applications like your CRM or HR system.
- Align Security with Classification: Map your security controls to your classification levels. For example, “Restricted” data should require multi-factor authentication and be encrypted both at rest and in transit, while “Public” data may not require such stringent protections.
- Train Employees and Audit Regularly: Conduct regular training to ensure staff understands the classification scheme and their role in protecting data. Periodically audit classifications to correct errors and refine your categories as business needs evolve.
8. Establish Vendor and Third-Party Data Handling Agreements with Clear Retention Requirements
Your data retention policy extends beyond your organization’s walls to any third-party vendor or partner with access to your information. Establishing clear, legally binding agreements that outline data handling and retention requirements is essential for maintaining control and compliance. These contractual provisions ensure that your vendors, from cloud storage providers to document shredding services, manage your data according to your internal policies and legal obligations, effectively closing potential gaps in your data governance strategy.
Without explicit vendor agreements, your data could be retained longer than necessary, mishandled, or improperly deleted, creating significant security and compliance risks. A Michigan healthcare provider, for instance, must ensure its cloud backup vendor adheres to HIPAA’s six-year retention minimum and provides certified data destruction afterward. These vendor requirements are a critical extension of your internal data retention policy best practices.
Why This Is a Core Best Practice
Formalizing vendor data handling requirements is crucial because it creates accountability and enforces consistency across your entire data ecosystem. It legally obligates your partners to uphold the same standards you do, protecting your organization from liability caused by a third party’s negligence. This practice provides a clear framework for auditing vendor compliance and a defined process for data disposition at the end of a contract, which is vital for minimizing your data footprint and reducing long-term risk.
How to Implement Vendor Agreements
Follow these actionable steps to ensure your third-party relationships are governed by strong data retention controls:
- Incorporate Data Retention Clauses: Work with legal counsel to embed specific data retention and disposal clauses directly into your vendor contracts. These should detail the exact retention periods for different data types they handle and mandate deletion upon contract termination or your request.
- Require Certification of Deletion: Contracts should obligate vendors to provide a formal certificate of destruction or a signed attestation once data has been securely and permanently deleted. This documentation is crucial for audit trails and demonstrating due diligence.
- Establish Audit Rights: Include clauses that give your organization the right to audit the vendor’s data handling and retention practices. This verification mechanism ensures they are not just agreeing to your terms but actively following them.
- Define Breach and Non-Compliance Terms: Clearly outline the vendor’s responsibilities for notifying you in the event of a data breach and define the specific consequences or penalties for failing to comply with the agreed-upon retention policies.
- Conduct Due Diligence: Before and during the partnership, review the vendor’s own data retention policies and security posture. This initial and ongoing vetting process helps ensure their practices align with your requirements from the start.
9. Plan for Data Disposal and Destruction Methods that Ensure Irretrievable Deletion
The final stage of the data lifecycle, secure disposal, is as critical as its creation and storage. An effective data retention policy must detail the specific methods for destroying data once it reaches the end of its retention period, ensuring it is permanently and irretrievably deleted. This process prevents unauthorized access to sensitive information on decommissioned hardware and media, which remains a significant security vulnerability for many organizations.
Simply deleting a file or reformatting a hard drive is insufficient, as the data can often be recovered with specialized tools. Formal destruction methods range from digital overwriting to physical shredding, and the chosen method must align with the data’s sensitivity and the media type. For Michigan businesses, especially those in healthcare or government, using certified and documented destruction processes is a non-negotiable compliance requirement.
Why This Is a Core Best Practice
Implementing a formal data destruction plan is a cornerstone of data retention policy best practices because it closes a critical security gap. Failing to properly destroy data leaves a trail of sensitive information that can be exploited, leading to data breaches, reputational damage, and severe regulatory fines. A documented destruction process provides a defensible audit trail, proving that your organization has acted responsibly to protect confidential information throughout its entire lifecycle, from creation to final disposition.
How to Implement Secure Data Destruction
Follow these actionable steps to integrate secure disposal into your data retention policy:
- Match Destruction Method to Data Sensitivity: Classify your data to determine the appropriate destruction technique. For public data, simple deletion might suffice. For confidential data like patient records or intellectual property, you must use methods like cryptographic erasure, multi-pass overwriting that meets the DOD 5220.22-M standard, or physical destruction.
- Select Certified Destruction Vendors: When outsourcing, partner with vendors who are certified in secure data destruction, such as those with R2 or e-Stewards certifications. These certifications ensure they follow strict environmental and data security protocols.
- Require Certificates of Destruction: Always demand a signed Certificate of Destruction from your vendor for every batch of media destroyed. This document serves as legal proof of secure disposal and should be retained as part of your compliance records.
- Document All Procedures: Your data retention policy should explicitly detail your destruction procedures, including the methods used for different data types and media, the vendors you use, and the documentation you require.
- Plan for Legacy and Modern Media: Create distinct procedures for destroying various media types, including hard drives (HDDs), solid-state drives (SSDs), magnetic tapes, optical discs, and mobile devices, as each requires a different approach for irretrievable deletion.
10. Align Data Retention Policies with Privacy, Security, and Data Minimization Principles
A modern data retention policy should not exist in a vacuum; it must be deeply integrated with broader privacy, security, and data minimization strategies. This approach treats data retention as a proactive security control rather than a passive administrative task. The core concept is simple: the less data you hold, the lower your risk of a breach, and the easier it is to manage compliance. Aligning these functions ensures that data is only kept for legitimate, documented business or legal purposes.
This best practice shifts the mindset from “how long can we keep this?” to “what is the absolute minimum time we need this?” For Michigan organizations, especially those in healthcare or government, this alignment is critical for demonstrating due diligence and adhering to privacy regulations that mandate purpose limitation and data minimization. It transforms the retention policy from a simple schedule into a dynamic part of your cybersecurity framework.
Why This Is a Core Best practice
Integrating retention with privacy and security is fundamental because it directly reduces your organization’s attack surface. Every piece of stored data, particularly sensitive information, represents a potential liability. By applying the principle of data minimization, you systematically shrink this liability. This practice also strengthens compliance with privacy laws like GDPR and HIPAA, which require that personal data processing be limited to what is necessary. It ensures a consistent, defensible rationale for every piece of data you store, simplifying audits and legal discovery.
How to Implement This Alignment
Follow these actionable steps to integrate your data retention policy with security and privacy principles:
- Conduct Privacy Impact Assessments (PIAs): Before collecting new types of data, perform a PIA to evaluate the necessity of collection and establish a clear business purpose. This assessment should directly inform the retention period assigned to that data category.
- Document the Business Purpose: For each data type in your retention schedule, clearly document the specific business or legal justification for its retention. Regularly review this purpose to confirm it is still valid; if not, the data should be securely destroyed.
- Embrace Anonymization and Pseudonymization: For data needed long-term for analytics or research, apply techniques to remove or obscure personal identifiers. A school district, for example, could anonymize student assessment data after its official retention period to use it for trend analysis without privacy risks.
- Integrate Governance Tools: For comprehensive data governance and to ensure your policies align with legal mandates for personal data, explore solutions like GDPR Compliant HR Software with Microsoft Purview Integration. These platforms help automate and enforce policies across your data estate.
- Coordinate Across Teams: Ensure that your IT security, legal, and compliance teams collaborate on defining retention rules. This cross-functional approach guarantees that policies are both technically sound and legally defensible. You can learn more about reducing cybersecurity risks with data minimization to strengthen this coordination.
10-Point Comparison: Data Retention Policy Best Practices
| Item | Implementation complexity | Resource requirements | Expected outcomes | Ideal use cases | Key advantages |
|---|---|---|---|---|---|
| Define Clear Retention Schedules Based on Business Function and Compliance Requirements | Medium–High — cross‑functional analysis and legal input | Legal counsel, records managers, time for data inventory | Documented, auditable retention schedules; reduced legal risk | Regulated industries, multi‑unit organizations, audit preparation | Clear governance, regulatory alignment, simplified audits |
| Implement Automated Data Deletion and Archival Processes | High — systems integration and workflow design | Engineers, automation tools, integration testing, monitoring | Consistent enforcement, lower storage costs, auditable deletion trails | Large data volumes, heterogeneous environments, high consistency needs | Eliminates manual error, scalable enforcement, tamper‑evident logs |
| Establish Legal Hold Procedures for Litigation, Investigations, and Regulatory Inquiries | Medium — defined processes and override controls | Legal team, IT controls, notification/tracking tools | Preserved evidence with documented holds; defensible preservation | Litigation, investigations, regulatory inquiries | Prevents spoliation, documents custodian obligations and actions |
| Conduct Regular Data Audits and Retention Compliance Assessments | Medium — audit planning and sampling plus tooling | Audit tools, cross‑functional audit team, remediation resources | Identified gaps, demonstrated due diligence, remediation plans | Compliance validation, pre‑audit readiness, multi‑system environments | Early detection of issues, evidence of ongoing compliance efforts |
| Integrate Data Retention Policies with Backup and Disaster Recovery Systems | High — synchronized policies across storage tiers | Backup/DR engineers, testing environments, vendor coordination | Deletions persistent across backups/archives; fewer accidental restores | Organizations with complex backup/DR architectures, regulated data | Ensures true deletion, prevents inadvertent data restoration |
| Document Retention Policy Development and Custodian Training | Medium — policy drafting, approval, and training rollout | Policy writers, trainers, LMS or training resources, legal review | Consistent policy application; accountable custodians; auditable records | Organizations seeking governance maturity or with high staff turnover | Improves compliance through training, clear roles and documentation |
| Address Data Classification and Categorization to Enable Accurate Retention Decisions | High — taxonomy design and wide‑scale classification | Classification tools, data inventory effort, ongoing training | More precise retention rules, aligned security controls | Large datasets, sensitive information, privacy‑focused environments | Enables accurate retention, supports minimization and security |
| Establish Vendor and Third‑Party Data Handling Agreements with Clear Retention Requirements | Medium — contract updates and vendor assessments | Legal/contracts team, vendor audits, ongoing monitoring | Vendor alignment with retention obligations, audit rights enforced | Heavy third‑party/cloud usage, outsourced processing | Reduces third‑party retention risk, contractual enforcement and verification |
| Plan for Data Disposal and Destruction Methods that Ensure Irretrievable Deletion | Medium — method selection and verification processes | Destruction vendors/tools, certification procedures, documentation | Irretrievable deletion with proof of destruction | End‑of‑life media, high‑sensitivity data, regulated disposal needs | Prevents data recovery, provides certified evidence of destruction |
| Align Data Retention Policies with Privacy, Security, and Data Minimization Principles | Medium — policy integration and ongoing review | Privacy/security teams, PIA capability, governance and training | Reduced breach exposure, privacy‑by‑design retention, fewer regulated holdings | Privacy‑sensitive organizations, GDPR/CCPA contexts, security‑centric firms | Lowers exposure, supports compliance and data minimization practices |
Transforming Your Data Policy from a Document into a Daily Practice
Navigating the complexities of data retention is no longer a task reserved for enterprise legal departments; it is a foundational component of modern business operations. Moving from a theoretical policy document to a functional, automated, and ingrained practice is the ultimate goal. The data retention policy best practices detailed throughout this guide are not independent checklist items. Instead, they are interconnected pillars that support a robust and defensible data governance strategy.
A successful data retention program hinges on treating it as a continuous cycle, not a one-time project. It begins with the foundational work of data classification and creating clear retention schedules tailored to both business needs and compliance mandates, from HIPAA to specific Michigan state regulations. These schedules are then brought to life through automation, which removes human error and ensures that data is consistently archived or disposed of at the right moment. This entire framework is then integrated with your essential backup and disaster recovery systems, ensuring that what you keep is protected and what you discard is truly gone.
From Compliance Burden to Business Advantage
Adopting these data retention policy best practices transforms your approach from reactive compliance to proactive risk management. By implementing formal legal hold procedures, you are always prepared for litigation or regulatory inquiries, avoiding costly sanctions and frantic data-gathering exercises. Similarly, establishing clear vendor management protocols and secure data destruction methods protects your organization from third-party risks and ensures that your data lifecycle is secure from creation to final deletion.
The most critical takeaways from this guide are:
- Automation is Your Ally: Manual processes are prone to error and inconsistency. Automating deletion and archival based on your defined policies is the single most effective step toward ensuring compliance and reducing data bloat.
- People are Your Perimeter: A policy is only as strong as the people who follow it. Comprehensive documentation and ongoing training are non-negotiable. Your team must understand their role in protecting and managing company data.
- Auditing Creates Accountability: You cannot manage what you do not measure. Regular audits and compliance assessments provide the necessary feedback to identify gaps, refine processes, and demonstrate due diligence to regulators and stakeholders.
Ultimately, a well-executed data retention policy is a powerful business enabler. It minimizes your digital footprint, which in turn reduces storage costs and shrinks the potential attack surface for cyber threats. It streamlines operations by ensuring employees can find the information they need without wading through obsolete data. For Michigan organizations in regulated sectors like healthcare, government, or manufacturing, mastering these practices is not just good business, it is essential for survival and growth. By treating your data retention policy as a living, breathing part of your organization’s culture, you build resilience, foster trust, and create a secure foundation for the future.
Ready to move from policy to practice? The experts at Kraft Business Systems specialize in creating integrated solutions-from secure document management and automated backup to managed IT and cybersecurity-that turn your data retention goals into a reality. Contact Kraft Business Systems to build a compliant, efficient, and secure data management framework for your Michigan organization.