Protecting your organization’s digital assets requires a multi-layered strategy, not just a single tool. Understanding the various security measures available is the first step toward building a resilient defense against cyber threats. For Michigan organizations, especially those in sectors like healthcare and manufacturing, implementing the right combination of security controls is crucial for maintaining operations, protecting sensitive data, and meeting regulatory requirements like HIPAA.
The digital environment is fraught with risks that can have severe financial and reputational consequences. To fully appreciate the need for robust network security, consider recent incidents such as the rising threat of infostealer malware, where millions of sensitive financial records were compromised. Such events highlight why a reactive approach to cybersecurity is no longer sufficient; a proactive, comprehensive defense is essential for survival and growth.
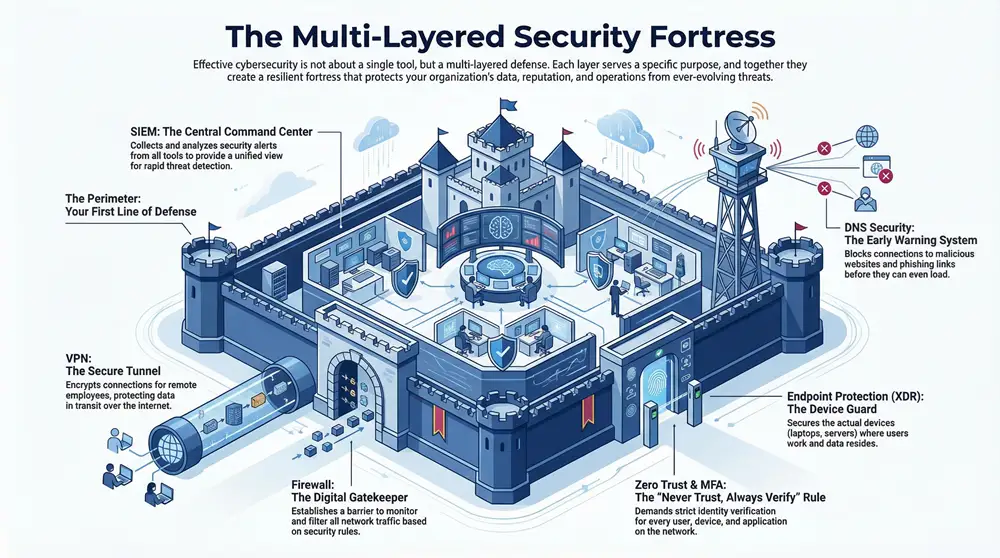
This guide breaks down ten essential different types of network security, providing clear explanations and practical steps to help you secure your infrastructure effectively. From foundational firewalls and intrusion detection systems to advanced Zero Trust models and endpoint protection, each component plays a vital role in a comprehensive security posture. You will learn not just what these technologies are, but how they work together to create a layered defense tailored to the specific challenges faced by small and mid-sized businesses. Our goal is to equip you with the knowledge to make informed decisions, whether you are strengthening your current defenses or building a new security framework from the ground up.
1. Firewall (Network Perimeter Security)
A firewall serves as the primary digital gatekeeper for your network. It’s a foundational security device that establishes a barrier between your trusted internal network and untrusted external networks, such as the public internet. By monitoring and controlling all incoming and outgoing network traffic, it acts based on a predefined set of security rules to permit or block data packets. This meticulous filtering is a critical first step in preventing unauthorized access and cyber threats from ever reaching your internal systems.
This technology is an essential component among the different types of network security because it provides a centralized point of control for enforcing security policies at the network’s edge.
Implementation and Best Practices
For a Michigan-based healthcare provider, a properly configured firewall is a non-negotiable part of HIPAA compliance. It helps protect electronic protected health information (ePHI) by blocking access from unauthorized sources. Similarly, a manufacturing firm can use firewalls to segment its corporate network from the operational technology (OT) network on the factory floor, preventing a breach in one area from spreading to another.
Here are actionable tips for effective firewall management:
- Adopt a “Default-Deny” Policy: This approach blocks all traffic by default and only permits connections that are explicitly allowed. This is significantly more secure than an “allow-all” policy that only blocks known threats.
- Regular Rule Audits: Routinely review and update your firewall rules to remove outdated or unnecessary entries. This closes potential security gaps and ensures the configuration aligns with current business needs.
- Filter Egress Traffic: Don’t just monitor incoming traffic. Filtering outgoing (egress) traffic can prevent malware from communicating with its command-and-control servers or stop data exfiltration.
- Enable Logging and Alerts: Actively monitor firewall logs for suspicious activity and configure alerts for policy violations. This proactive monitoring enables rapid response to potential security incidents.
A well-managed firewall is more than just a piece of hardware; it’s a dynamic and active defense mechanism. To see how professional oversight can enhance this critical security layer, you can explore the benefits of a managed firewall service.
2. Intrusion Detection System (IDS) / Intrusion Prevention System (IPS)
If a firewall is the digital gatekeeper, an Intrusion Detection System (IDS) and Intrusion Prevention System (IPS) act as the vigilant security guards patrolling your network’s interior. These security tools continuously monitor network traffic for malicious activity and policy violations. An IDS identifies potential threats and generates alerts for security administrators, while an IPS takes the next step by actively blocking or preventing the detected threats in real-time. This combination provides a crucial layer of active defense that complements a firewall’s perimeter control.
These systems are a vital element among the different types of network security because they provide visibility into traffic after it has passed the firewall, identifying threats that may have otherwise gone unnoticed. They use signature-based methods to spot known attack patterns and anomaly-based detection to flag unusual behavior that deviates from a normal baseline.
Implementation and Best Practices
For a Michigan school district, an IPS can be instrumental in blocking students from accessing prohibited applications or websites, enforcing acceptable use policies automatically. A local government agency can use an IDS to monitor for signs of a ransomware attack, such as unusual file access patterns, allowing for a swift response before significant damage occurs. These systems provide the deep traffic inspection needed to detect sophisticated threats.
Here are actionable tips for effective IDS/IPS management:
- Tune Detection Rules: Actively manage and customize rules to minimize “false positives” (legitimate traffic flagged as malicious). This ensures your security team focuses on genuine threats without being overwhelmed by irrelevant alerts.
- Update Threat Signatures Constantly: Attack methods evolve rapidly. Ensure your IDS/IPS signature database is updated regularly, ideally automatically, to recognize the latest malware, exploits, and vulnerabilities.
- Combine Detection Methods: Don’t rely solely on signatures. Implement anomaly-based detection by establishing a clear baseline of normal network traffic. This allows the system to identify new, unknown, or zero-day threats.
- Strategic Placement: Deploy IDS/IPS sensors at critical network choke points, such as behind the firewall, in front of key server farms, or at the boundary of a sensitive network segment, to maximize visibility and protection.
3. Virtual Private Network (VPN)
A Virtual Private Network (VPN) creates a secure, encrypted connection over a less secure network, such as the public internet. This technology essentially builds a private, protected “tunnel” for your data to travel through, shielding it from unauthorized interception and snooping. By masking your IP address and encrypting all traffic between a user’s device and the network, a VPN allows remote employees and branch offices to access corporate resources as securely as if they were physically connected to the main office.
This method is a cornerstone among the different types of network security because it extends the secure perimeter of your network to wherever your employees are, enabling safe remote work and protecting data in transit.
Implementation and Best Practices
For a Michigan law firm with attorneys working from home or in court, a VPN is essential for securely accessing sensitive client files, meeting compliance standards for data privacy. Likewise, a financial services company can use a site-to-site VPN to securely connect its main office with a smaller branch, ensuring that all data shared between locations remains confidential and integral.
Here are actionable tips for effective VPN management:
- Enforce Multi-Factor Authentication (MFA): A password alone is not enough. Implementing MFA for VPN access adds a critical layer of security, requiring a second form of verification to prevent unauthorized users from gaining entry with stolen credentials.
- Use Strong Encryption Standards: Always configure your VPN to use robust encryption protocols like AES-256. Weak encryption can be compromised, rendering the VPN tunnel ineffective against determined attackers.
- Keep VPN Software Updated: Cybercriminals actively look for vulnerabilities in VPN clients and servers. Regularly updating all VPN software to the latest version is crucial for patching security holes and protecting your network.
- Implement a “No-Logs” Policy: When using a third-party VPN service, choose a reputable provider with a strict, independently audited no-logs policy. This ensures that your online activities are not recorded or stored, maximizing privacy.
A properly configured VPN is a powerful tool for enabling a flexible and secure workforce. It transforms the public internet into a secure extension of your private network. To ensure your remote access is both secure and compliant, learn more about implementing robust cybersecurity solutions.
4. Multi-Factor Authentication (MFA) / Two-Factor Authentication (2FA)
Multi-Factor Authentication adds a critical layer of verification to your access controls, going beyond a simple password. It requires users to present two or more independent credentials before gaining entry to an application, account, or network. This process typically combines something you know (a password), something you have (a smartphone app or hardware token), and something you are (a fingerprint or face scan). By requiring this additional evidence of identity, MFA makes it exponentially more difficult for unauthorized users to gain access, even if they have stolen a password.
This method is a cornerstone among the different types of network security because it directly addresses the weakness of password-only systems, which are highly susceptible to phishing, brute-force attacks, and credential stuffing.
Implementation and Best Practices
For a Michigan-based government agency handling sensitive citizen data, implementing MFA for all remote access points is a fundamental security control. Likewise, a K-12 school district can use MFA to protect student information systems and teacher accounts from unauthorized access, safeguarding confidential records. This simple step can prevent a wide range of security incidents initiated by compromised credentials.
Here are actionable tips for effective MFA deployment:
- Mandate for Critical Access: Enforce MFA for all administrative accounts, remote access (like VPNs), and access to critical applications or data. These are high-value targets for attackers.
- Prioritize Authenticator Apps: Whenever possible, use app-based authenticators (like Google Authenticator or Microsoft Authenticator) over SMS-based codes. SMS is vulnerable to SIM-swapping attacks.
- Educate Your Users: Train employees on what MFA is, why it’s important, and how to use it correctly. This education reduces friction and improves adoption rates across the organization.
- Implement Adaptive Authentication: Consider risk-based or adaptive MFA, which can require stronger verification methods when a user logs in from an unfamiliar location or device, creating a smarter security posture.
5. Data Loss Prevention (DLP)
Data Loss Prevention (DLP) is a strategic set of tools and processes designed to stop sensitive information from leaving your organization without authorization. It works by identifying, monitoring, and protecting data in use, data in motion across your network, and data at rest in your storage. DLP systems use deep content inspection and contextual analysis to enforce predefined policies, automatically blocking or flagging unauthorized attempts to share confidential information via email, cloud storage, or physical devices.
This technology is a critical component among the different types of network security because it directly addresses the risk of data breaches caused by either malicious intent or accidental user error. It provides granular control over your organization’s most valuable asset: its data.
Implementation and Best Practices
For a financial services firm in Michigan, a DLP solution is essential for complying with regulations like the Gramm-Leach-Bliley Act (GLBA). It can automatically prevent an employee from accidentally emailing a client list containing non-public personal information (NPI) to an external address. Likewise, a manufacturing company can use DLP to protect proprietary blueprints and intellectual property from being uploaded to unauthorized cloud services or copied to a USB drive.
Here are actionable tips for effective DLP implementation:
- Define Clear Data Classification Policies: Before deploying a DLP tool, classify your data. Identify what is critical, confidential, and public. This ensures your policies protect what truly matters without disrupting normal business operations.
- Start in Monitoring-Only Mode: Begin by deploying DLP rules in a non-blocking, monitoring mode. This helps you understand how data flows within your organization and allows you to fine-tune rules to minimize false positives before you start enforcing them.
- Train Employees on Data Handling: Technology alone is not enough. Educate your staff on proper data handling procedures and the importance of security policies. Informed users are your first line of defense against accidental data loss.
- Balance Security with Productivity: Overly restrictive DLP policies can hinder employee productivity. Implement graduated response actions, such as user notifications and justifications for certain actions, rather than just blocking everything. This maintains security while enabling legitimate work.
An effective DLP strategy is about understanding and controlling your data. For guidance on creating a comprehensive data protection plan tailored to your industry’s specific needs, consider partnering with a managed security service provider.
6. Zero Trust Security Model
The Zero Trust security model fundamentally inverts the traditional “trust but verify” approach. It operates on the principle of “never trust, always verify,” assuming that threats can exist both outside and inside the network. This framework eliminates the outdated idea of a trusted internal network and an untrusted external one. Instead, it demands strict identity verification for every person and device trying to access resources on the network, regardless of their location.
This strategic approach is a crucial component among the different types of network security because it directly addresses the challenges of remote work, cloud services, and sophisticated insider threats. It mandates that no one is trusted by default, creating a more resilient defense against unauthorized access and data breaches. For a deeper dive into this paradigm, explore how a Zero Trust Architecture works in reinventing information security.
Implementation and Best Practices
For a Michigan-based legal firm managing sensitive client data, Zero Trust ensures that only the assigned attorney can access specific case files, even if they are working from home. A local government agency can use this model to grant a contractor access only to a single application they need, preventing lateral movement across the network to other sensitive systems.
Here are actionable tips for implementing a Zero Trust framework:
- Implement Identity-Centric Security First: Start by strengthening your identity and access management (IAM). Utilize multi-factor authentication (MFA) everywhere to ensure users are who they claim to be.
- Use Micro-segmentation: Break your network into small, isolated zones. This contains any potential breach to a small area, preventing an attacker from moving freely across your entire network.
- Map All Users and Resources: You cannot protect what you cannot see. Begin by identifying and mapping all your users, devices, applications, and data flows to understand access needs and patterns.
- Maintain Detailed Access Logs: Continuously monitor and log all access events. Analyzing these logs helps you detect anomalous behavior, enforce policies, and respond quickly to potential threats.
7. Security Information and Event Management (SIEM)
A Security Information and Event Management (SIEM) system serves as the central nervous system for your cybersecurity operations. It is a comprehensive solution that collects, aggregates, and analyzes log data and security alerts from across your entire IT infrastructure, including servers, firewalls, applications, and endpoint devices. By correlating this vast amount of information in real-time, a SIEM platform can identify patterns, anomalies, and potential security threats that would be impossible to spot in isolation. This centralized visibility is crucial for rapid threat detection and effective incident response.
This technology is a pivotal component among the different types of network security because it transforms raw security data into actionable intelligence, enabling organizations to move from a reactive to a proactive security posture.
Implementation and Best Practices
For a Michigan government agency handling sensitive citizen data, a SIEM is essential for maintaining compliance with regulations like NIST and CJIS. It provides the necessary audit trails and real-time monitoring to detect unauthorized access attempts or data breaches. Similarly, a local school district can use a SIEM to monitor network activity for signs of student data compromise or cyberbullying, providing a unified view of security events across multiple school buildings.
Here are actionable tips for effective SIEM implementation:
- Start with Core Data Sources: Begin by integrating logs from your most critical assets, such as firewalls, domain controllers, and key servers. Gradually expand to include other sources as your team becomes more proficient.
- Develop Custom Correlation Rules: Don’t rely solely on out-of-the-box rules. Create custom rules that align with specific threats relevant to your industry, such as detecting unusual access patterns to electronic protected health information (ePHI) in a healthcare setting.
- Tune to Reduce False Positives: SIEMs can generate a high volume of alerts. Regularly review and tune your rules to minimize “noise” from false positives, allowing your security team to focus on genuine threats.
- Establish Clear Incident Response Playbooks: Define and automate responses for common alerts. For instance, an alert for repeated failed logins from a specific IP address could trigger an automated playbook that temporarily blocks that IP.
A properly managed SIEM provides the holistic view needed to connect the dots between seemingly unrelated events. To understand how expert configuration and monitoring can maximize this investment, explore the advantages of a comprehensive cybersecurity service.
8. Network Segmentation (Micro-segmentation)
Network segmentation is an architectural security approach that divides a computer network into smaller, isolated sub-networks, or segments. Each segment acts as its own small network, allowing security teams to apply specific controls and policies to traffic that moves between them. This strategy drastically limits an attacker’s ability to move laterally across your network, effectively containing a breach to the initially compromised segment. Micro-segmentation takes this concept a step further by creating highly granular security zones, sometimes as small as a single workload or application, to enforce a zero-trust security model.
This method is a crucial component among the different types of network security because it moves away from a hard perimeter and soft interior model. By assuming a breach could happen anywhere, it builds internal defenses that minimize the potential impact and prevent a minor intrusion from escalating into a major incident.
Implementation and Best Practices
For a Michigan manufacturing firm, segmenting the corporate IT network from the operational technology (OT) network on the factory floor is a prime example. This ensures that a malware infection on an office computer cannot disrupt critical production machinery. Similarly, a healthcare provider can use micro-segmentation to isolate systems containing electronic protected health information (ePHI), creating a secure enclave that meets strict HIPAA compliance requirements by severely restricting access.
Here are actionable tips for effective network segmentation:
- Map and Classify Assets: Begin by identifying and categorizing all assets on your network. Understand what data they process and their level of criticality to prioritize which areas to segment first.
- Implement Least Privilege Access: Configure rules between segments based on the principle of least privilege. A user or application in one segment should only have the absolute minimum access required to function with another segment.
- Monitor at Segment Boundaries: Deploy security tools, such as internal firewalls or intrusion detection systems, at the boundaries of each segment. This provides visibility into inter-segment traffic and helps detect suspicious lateral movement.
- Test and Document Policies: Before deploying segmentation policies in a live environment, test them thoroughly to avoid disrupting business operations. Maintain clear documentation for all segmentation rules and network architecture.
Implementing segmentation creates a more resilient and defensible network. To navigate the complexities of this advanced strategy, a network security assessment can provide the blueprint for a successful deployment.
9. Endpoint Protection / Extended Detection and Response (XDR)
Endpoint protection secures the individual devices that connect to your network, such as computers, servers, and mobile phones. These devices, or endpoints, are often the primary targets for cyberattacks. Modern security has evolved from traditional antivirus to Extended Detection and Response (XDR), a unified approach that integrates data from multiple security layers, including endpoints, email, and cloud applications, to provide holistic threat visibility and coordinated response actions. This centralized view allows for faster detection of sophisticated threats that might otherwise go unnoticed.
This advanced defense is a critical component among the different types of network security because it moves protection beyond the network perimeter directly to the devices where users work and data resides. By correlating threat intelligence across the entire IT environment, XDR platforms can automatically contain threats on an endpoint before they spread across the network.
Implementation and Best Practices
For a Michigan law firm managing sensitive client data, deploying an XDR solution ensures that a single compromised laptop doesn’t lead to a full-scale data breach. The platform can automatically isolate the device, analyze the threat, and provide a clear remediation path. Similarly, a local school district can use endpoint protection to secure student and faculty devices, preventing ransomware from disrupting educational activities, whether the devices are on or off campus.
Here are actionable tips for effective endpoint security management:
- Deploy Consistently: Ensure that your chosen endpoint protection agent is installed and active on every single company-owned device, including servers and mobile devices, to eliminate blind spots.
- Keep Intelligence Updated: Regularly update threat intelligence feeds, signatures, and behavioral detection engines. Automated updates are crucial for defending against zero-day vulnerabilities and emerging malware.
- Configure and Tune Alerts: Set appropriate alert thresholds to minimize false positives while ensuring that genuine threats trigger immediate notifications. Fine-tuning these settings prevents alert fatigue for your IT team.
- Integrate with SIEM: Feed endpoint data into your SIEM platform. This allows for the correlation of endpoint events with network logs and other security data, providing a richer context for incident investigation.
A robust endpoint strategy is essential for protecting a distributed workforce. To understand how this extends to mobile devices, you can read about the necessity of mobile device management for a complete security posture.
10. DNS Security and Threat Intelligence
DNS Security is a proactive approach that turns the internet’s address book, the Domain Name System (DNS), into a powerful security control point. Every time a user clicks a link or types a web address, their device sends a DNS query to find the corresponding IP address. DNS security intercepts these queries and checks the requested domain against a constantly updated list of known malicious sites, such as those used for phishing, malware distribution, or command-and-control (C&C) communication. If a domain is flagged as dangerous, the connection is blocked before it can even be established, effectively stopping the threat at the earliest possible stage.
This method is one of the most efficient types of network security because it prevents users from ever reaching harmful destinations. By leveraging real-time threat intelligence feeds, it provides an agile and adaptive layer of defense against emerging threats without requiring software installation on every endpoint device.
Implementation and Best Practices
For a Michigan school district, DNS filtering is a cost-effective way to enforce content policies and block students from accessing malicious or inappropriate websites on the school network. A local government agency can use it to prevent employees from falling victim to phishing attacks that could lead to a ransomware incident, protecting sensitive citizen data by stopping malicious links from ever resolving.
Here are actionable tips for implementing DNS security:
- Filter at the Gateway: Configure your network router or gateway to use a secure DNS service. This ensures all devices on your network are protected automatically, without individual configuration.
- Leverage Threat Intelligence: Use DNS services that are powered by reputable and continuously updated threat intelligence feeds. This is crucial for blocking new and emerging threats.
- Log and Analyze Queries: Enable DNS query logging to gain visibility into your network’s traffic patterns. Monitoring these logs can help identify compromised devices or policy violations.
- Enable DNSSEC: Implement DNS Security Extensions (DNSSEC) where possible. This cryptographic feature validates that DNS responses are authentic and have not been tampered with, preventing DNS spoofing and cache poisoning attacks.
By turning a fundamental internet protocol into a security tool, you can significantly reduce your organization’s attack surface. To understand how this fits into a broader defense strategy, you can explore the role of a managed security service provider in threat intelligence.
Top 10 Network Security Types Comparison
Building Your Security Strategy with a Michigan-Focused Partner
Navigating the diverse world of network security can feel like assembling a complex puzzle without the final picture. We have explored ten critical layers of defense, from the foundational role of firewalls and VPNs to the advanced, proactive stances of a Zero Trust model and SIEM systems. Each of these different types of network security represents a vital piece of a holistic strategy designed to protect your organization’s most valuable assets: its data, its reputation, and its continuity.
The core takeaway is that modern cybersecurity is not about choosing a single, magic-bullet solution. Instead, it is about building a multi-layered, resilient defense. A firewall alone is no longer sufficient. It must be supported by Intrusion Detection and Prevention Systems (IDS/IPS) to spot threats that slip past the perimeter. Endpoint protection is essential to secure the devices your employees use daily, while DNS security and threat intelligence act as your early-warning system, blocking malicious domains before they can ever load.
For Michigan-based organizations, especially those in regulated sectors like healthcare and manufacturing, this layered approach is non-negotiable. The challenge isn’t just implementing these tools; it’s ensuring they work together harmoniously, share intelligence, and provide a unified view of your security posture.
From Theory to Action: Key Strategic Imperatives
Understanding the concepts is the first step, but putting them into practice is what truly secures your business. As you move forward, prioritize these strategic actions:
- Embrace Layered Defense: Don’t rely on a single technology. The strength of your security comes from the integration of multiple controls. A threat that bypasses your firewall might be caught by your IDS/IPS or blocked at the endpoint by an XDR solution.
- Prioritize Identity and Access: Tools like Multi-Factor Authentication (MFA) are no longer optional. They are one of the most cost-effective and powerful controls you can implement to prevent unauthorized access, which is the root cause of the vast majority of data breaches.
- Assume Breach, Verify Everything: The Zero Trust model is more than a buzzword; it’s a fundamental shift in security philosophy. By operating on the principle of “never trust, always verify,” you drastically reduce the potential for lateral movement by an attacker who gains initial access. This is where network segmentation and a robust identity framework become critical.
- Gain Visibility and Respond Quickly: You cannot protect what you cannot see. Solutions like SIEM and XDR provide the necessary visibility into what’s happening across your network. More importantly, they enable a rapid, coordinated response to contain threats before they can escalate into a full-blown crisis.
Why a Local Partner Matters for Michigan Businesses
The operational realities for a healthcare provider in Grand Rapids dealing with HIPAA compliance are vastly different from a manufacturing firm in Detroit securing its supply chain data. This is where a local, specialized partner provides an unmatched advantage. A Michigan-based expert understands the specific regulatory environment, the regional threat actors, and the economic pressures facing local businesses.
Implementing and managing the different types of network security is a full-time job requiring deep expertise, continuous monitoring, and constant adaptation. For small and mid-sized organizations, building an in-house team with this level of skill is often impractical and cost-prohibitive. Partnering with a managed security service provider (MSSP) allows you to gain access to enterprise-grade tools and a dedicated team of security professionals for a predictable, manageable cost. This allows your team to focus on core business objectives, confident that your digital infrastructure is protected by experts who are right in your backyard.
Your network is the lifeblood of your organization. Protecting it is not just an IT task; it is a fundamental business imperative that underpins your success, growth, and resilience in a constantly evolving digital world.
Ready to move from understanding the concepts to implementing a robust, layered security strategy for your Michigan organization? The team at Kraft Business Systems specializes in designing, deploying, and managing comprehensive security solutions that cover all the different types of network security discussed in this article. Let us help you build a defense that is tailored to your unique needs, industry regulations, and budget.