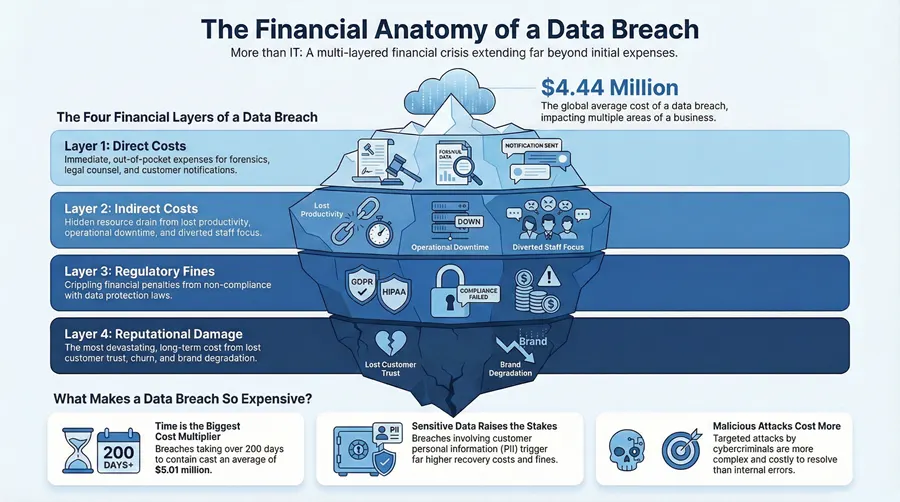
A data breach isn’t just a technical glitch—it’s a full-blown financial crisis waiting to happen. The latest numbers show the global average cost of a data breach is a staggering $4.44 million. That figure isn’t just one big invoice; it’s the total financial footprint left behind, from the immediate scramble to clean up the mess to the slow, painful erosion of customer trust.
What a Data Breach Really Costs Your Business
To get your head around the true price tag of a security incident, you have to look beyond a single number. The total cost is a combination of many different expenses that pop up over time, hitting multiple areas of your business and creating a massive, often unexpected, financial strain.
It’s critical to understand the severe impact of security breaches and why they simply can’t be ignored. The financial fallout goes far beyond the initial IT bill for containment.
The Financial Ripple Effect
A breach sets off a chain reaction of expenses. First, you’ve got the immediate costs of detection and response—think hiring forensic experts to figure out how deep the rabbit hole goes. Right after that, you’re hit with the costs of notifying customers, offering credit monitoring services, and hiring a PR team to manage the reputational damage.
The numbers in this environment can be volatile. After hitting an all-time high of $4.88 million, the global average recently dipped back down to $4.44 million. Likewise, the average cost per compromised record saw a small drop from $165 to about $160—still a massive liability for any organization holding customer data.
But this first wave of spending is just the warm-up act. The long-term costs, the ones that sneak up on you, are often what do the most damage to your bottom line.
A High-Level View of Cost Categories
To make sense of the financial damage, it helps to break the expenses down into a few major buckets. Each category lines up with a different phase of the breach, from the moment you find out it happened to the long, slow road to recovery.
A classic mistake is fixating on the obvious expenses like IT overtime and legal consultations. The real sting comes from the hidden costs—lost business opportunities and a tarnished brand that can haunt you for years.
To give you a clearer picture, the table below breaks down the main financial components that add up to the total cost of a data breach. This framework shows how a single event can hit so many different parts of a company’s financial health.
Quick Look at Key Data Breach Cost Categories
| Cost Category | Description | Examples |
|---|---|---|
| Direct Costs | Immediate, out-of-pocket expenses required to contain and remediate the breach. | Forensic investigation, hiring IT contractors, PR firm retainers, customer notification letters, setting up a call center, credit monitoring services. |
| Indirect Costs | Hidden or internal costs that aren’t as obvious but drain resources and productivity. | Employee overtime, internal investigation time, productivity loss, business downtime, operational disruptions. |
| Lost Business | The financial impact of customer churn and reputational damage following a breach. | Lost sales from existing customers, failure to acquire new customers, increased customer acquisition costs, brand degradation. |
| Regulatory Fines | Penalties and fines levied by government bodies for non-compliance with data protection laws. | HIPAA fines (for healthcare), GDPR penalties (for EU data), PCI-DSS fines (for credit card data), state-level privacy law violations. |
As you can see, the costs are multifaceted. Focusing only on the direct expenses is like only looking at the tip of the iceberg—the real danger lies beneath the surface.
The Four Financial Layers of a Security Incident
When you’re staring down a data breach, it’s easy to focus on the immediate, tangible expenses. But the true cost isn’t a single invoice; it’s more like an onion. You have to peel back four distinct layers of financial damage, and each one stings more than the last, revealing just how deeply a security incident can cut into your business.
The total bill adds up quickly, and as you’ll see, the expenses go far beyond just fixing the initial technical glitch.
This breakdown makes one thing painfully clear: the biggest hit often comes from lost business, a consequence that can linger for years.
Layer 1: Direct Costs
These are the obvious, in-your-face expenses that show up right away. Think of them as the emergency room bill for your data. They are the immediate, out-of-pocket payments you have to make just to stop the bleeding.
First, you’ll be calling in the experts. Forensic investigators need to figure out how the attackers got in and what they took. You’ll need legal counsel to navigate the mess, and likely a PR firm to handle the inevitable public fallout. These services aren’t cheap and demand payment now.
Then come the other immediate financial hits:
- Customer Notifications: You’re legally required to inform everyone affected, which means paying for drafting, printing, and mailing thousands of letters.
- Call Center Support: You’ll need to set up a dedicated call center to field the flood of calls from worried customers.
- Credit Monitoring: Offering free credit monitoring and identity theft protection to victims has become standard practice, and those per-person monthly fees add up fast.
Layer 2: Indirect Costs
If direct costs are a punch to the gut, indirect costs are the slow internal bleeding that follows. These expenses don’t come with a neat invoice, but they quietly drain your company’s resources and kill momentum. Your team’s focus shifts overnight from growth and innovation to pure damage control.
Productivity grinds to a halt. Your IT team will be pulling all-nighters just to contain the threat and get systems back online. Meanwhile, your leadership and marketing teams are sucked into crisis meetings, completely derailing their strategic work.
The most underestimated indirect cost is operational downtime. Every minute your systems are offline or your employees are unable to work is a direct hit to your revenue and momentum.
This disruption is a massive part of the total cost and can drag on for months. Having a well-rehearsed plan for security incident management is the only way to minimize this downtime and get a handle on these hidden expenses. Our full guide can walk you through building one from the ground up.
Layer 3: Regulatory Fines
Now we get to the punitive layer. Depending on your industry and the data that was stolen, you could be facing staggering regulatory fines. These penalties aren’t just designed to sting; they’re designed to send a message about non-compliance.
For instance, healthcare providers who expose patient records get hit with massive fines under HIPAA. If you handle data from European citizens, you’re under the thumb of GDPR. These fines can easily climb into the seven-figure range.
Don’t mistake these for a simple slap on the wrist—they are meant to be financially crippling. In fact, organizations with poor compliance practices face significantly higher breach costs, averaging a brutal $4.62 million per incident.
Layer 4: Reputational Damage
This is the final, and often most devastating, layer. Reputational damage is the long-term erosion of trust, and once it’s gone, it’s incredibly difficult and expensive to earn back. Customers who feel you failed to protect their data will simply take their business elsewhere. Period.
A tarnished brand leads to a sustained drop in sales and makes attracting new customers a tough, uphill battle. This impact is felt long after the technical fires are out and the fines are paid. Consider this: hospitals spend 64% more on advertising in the two years following a breach just to try and repair their public image.
This long-tail cost is frequently the most significant and enduring financial consequence of a security failure.
What Makes a Data Breach So Expensive?
Not every data breach is a front-page catastrophe. Some are minor bumps in the road, while others can become full-blown financial disasters that threaten a company’s survival. The final bill for a breach isn’t random; a few key factors act as cost multipliers, turning a manageable incident into an incredibly expensive ordeal.
If you want to spend your security budget wisely, you need to understand what really drives these costs up.
The single biggest factor? Time. Think of a data breach like a slow water leak inside your office walls. Catch it on day one, and you’re just patching a small hole. But if that leak goes unnoticed for six months, you’re not just fixing a pipe anymore—you’re dealing with rotted studs, ruined drywall, and a massive mold problem. The damage quietly spreads, and the repair bill skyrockets.
The High Price of a Slow Response
A delayed response is an open invitation for attackers to dig deeper into your network, steal more data, and cause far more damage. The financial gap between a fast and a slow reaction is staggering.
While global breach costs have stabilized a bit, the price tag for just detecting and escalating the problem still averages a painful $1.47 million. The real kicker, though, is how that number changes with time. Breaches that take longer than 200 days to find and contain end up costing an average of $5.01 million. That’s a massive financial penalty for slow detection. You can dig deeper into how timelines impact expenses by reading these data breach statistics.
This is why having proactive network monitoring and a well-rehearsed incident response plan isn’t just a “nice-to-have.” Every single day you shave off your detection and containment time translates directly into millions of dollars saved.
The moment a breach is suspected, the clock starts ticking. The speed and efficiency of your response will directly determine whether the incident is a manageable event or a company-defining crisis.
The Type of Data Stolen Matters—A Lot
Another major cost driver is the type of data that gets compromised. There’s a world of difference between losing some internal operational files and losing your customers’ personal information.
When we talk about high-value data, we mean Personally Identifiable Information (PII). This is the sensitive stuff: names, addresses, Social Security numbers, driver’s licenses. When this kind of data is stolen, the stakes—and the costs—shoot through the roof.
Here’s why:
- Strict Regulatory Requirements: Laws like HIPAA for healthcare and GDPR in Europe don’t just suggest you protect PII; they demand it. Violations come with heavy fines and mandatory, expensive notification procedures.
- Higher Recovery Costs: Suddenly, you’re on the hook for services like credit monitoring and identity theft protection for every single person affected. Those costs add up fast.
- Greater Reputational Damage: Customers are far less forgiving when their personal data is exposed. A breach of PII almost always leads to a higher rate of customer churn and a tougher road to regaining trust.
It’s no surprise that breaches involving health or financial records are consistently the most expensive. The potential for real harm to individuals is so high that it triggers the costliest legal and recovery actions.
Your Industry and the Attacker’s Motive
Finally, your industry and the root cause of the breach play a huge role in the final bill. Some sectors are just more expensive targets. Healthcare, for instance, has held the unfortunate title of the costliest industry for a data breach for over a decade. The extreme sensitivity of patient data, combined with strict HIPAA regulations, means their average breach cost often dwarfs that of other industries. Finance and pharmaceuticals aren’t far behind.
The origin of the breach is the last big variable. A targeted, malicious attack from a sophisticated cybercriminal group is going to cost you a lot more to fix than an incident caused by an employee mistake or a simple system glitch. Malicious attacks are harder to investigate, tougher to contain, and often involve destructive tools like ransomware that add entirely new layers of complexity and expense to the recovery.
Understanding these key cost drivers is the first step in preparing for the financial reality of a modern security incident.
How Proactive Strategies Can Lower Breach Costs
The total cost of a data breach isn’t some fixed, unavoidable penalty. It’s a direct reflection of how prepared you are. Smart, proactive investments in your security can dramatically slash the potential financial damage, turning a potential catastrophe into a manageable business challenge.
It really comes down to focusing on a few key areas that deliver the biggest return on your investment. This is all about building a resilient defense rather than just reacting to an attack after the damage is already done.
This strategic approach is critical because the financial hit from a breach comes fast and hard. In fact, a staggering 51 percent of all costs pile up in the first year after an incident. That number alone highlights the immediate financial shock you’ll face.
Build and Practice an Incident Response Plan
Your single most effective defense against skyrocketing breach costs is a well-practiced Incident Response (IR) plan. Think of it as a fire drill for a cyberattack. Without a plan, your team will waste precious time and resources scrambling to figure out what to do, all while the breach deepens and costs multiply.
A strong IR plan outlines exactly who does what, when, and how. It’s a clear, step-by-step roadmap for identifying, containing, and getting rid of a threat. That clarity minimizes downtime, prevents panic-driven mistakes, and speeds up recovery like nothing else.
An Incident Response plan isn’t a document you create once and file away. Its value comes from regular testing and refinement, ensuring your team can execute it flawlessly under pressure.
Organizations with a tested IR plan consistently see lower breach costs because they stop the bleeding faster. They spend less on containment and recovery, and they restore customer confidence much more quickly.
Use Cyber Insurance as a Financial Safety Net
Cyber insurance is another critical tool for managing the financial fallout of a data breach. While it won’t stop an attack from happening, it acts as a crucial financial safety net to help your business recover without staring down insolvency.
It’s essential, however, to understand what these policies actually cover. Typically, coverage includes:
- Direct Costs: Expenses for things like forensic investigations, legal counsel, and customer notifications.
- Regulatory Fines: Financial penalties from bodies like HIPAA or for GDPR non-compliance.
- Business Interruption: Compensation for lost revenue while your operations are down.
But let’s be clear: cyber insurance is not a substitute for strong security. In fact, most insurers now require businesses to prove they have a solid security posture before they’ll even offer a policy. Think of it as a complementary strategy that helps transfer some of that financial risk.
Make Data Backups Your Ransomware Defense
Ransomware attacks are a primary driver of those horrifyingly high data breach costs. When your critical files are encrypted and held hostage, the pressure to pay the ransom can be immense. Reliable, tested data backups are your ultimate defense against this kind of extortion.
Having secure, isolated backups turns a potential disaster into a manageable inconvenience. Instead of negotiating with criminals, you can simply wipe the affected systems and restore your data from a clean copy. This move not only saves you from paying a ransom but also dramatically cuts down on your recovery time. As part of a holistic approach, implementing robust strategies like secure hard drive recycling can also safeguard sensitive information and prevent future liabilities.
Partner with Cybersecurity Experts
Finally, the highest return on investment comes from preventing breaches in the first place. For many small and mid-sized businesses, partnering with a managed cybersecurity provider offers the expertise and tools needed to build a strong defense.
These experts provide the kind of continuous monitoring, threat detection, and proactive maintenance that most internal IT teams simply can’t match. By identifying and neutralizing threats before they can cause damage, you avoid the breach—and all its associated costs—entirely. This preventative approach is the foundation of a resilient and financially secure organization. For more actionable steps, check out our guide on data breach prevention tips that your team can implement.
Calculating Your Organization’s Potential Exposure
Knowing what a data breach could cost is one thing. Figuring out what it would cost your business is the next critical step. This is where we move from theory to action, putting a real number on your potential financial risk. Don’t worry, you don’t need a PhD in statistics; this starts with an honest look in the mirror.
Think of it as a financial stress test for your cybersecurity. The whole point is to come up with a realistic, data-backed estimate. This number becomes the foundation for serious conversations about your security budget, risk management, and overall defense strategy. It stops you from guessing about the damage and gets you started on a real plan.
A Simplified Framework for Your Internal Assessment
To get a ballpark estimate of your exposure, you need to size up a few key factors unique to your business. We’re not aiming for a perfect, down-to-the-penny figure here. The goal is a directional estimate that paints a clear picture of your specific risk profile.
Start by pulling together some basic information:
- Data Sensitivity and Volume: What kind of data are you holding, and how much of it do you have? The price tag for losing sensitive PII or protected health information (PHI) is way higher than for generic operational data.
- Industry and Regulatory Requirements: Are you in a heavily regulated field like healthcare or finance? If so, you have to factor in the potential for massive fines from non-compliance with rules like HIPAA, which can send the total cost of a breach through the roof.
- Current Security Measures: Be honest about your defenses. Do you have a documented incident response plan? Do you train your staff to spot phishing emails? The stronger your security posture is right now, the lower your potential costs will be.
- Customer Base Size: How many people would you have to notify if you were breached? Every single notification letter, every call to a help desk, and every credit monitoring subscription adds a direct, per-person cost to the final tally.
The most eye-opening part of this whole exercise is realizing that data breach costs aren’t some fixed, unavoidable number. They are directly shaped by the decisions you make before an incident ever happens—from the security tools you invest in to the data you decide to keep.
Turning Your Assessment into Actionable Next Steps
Once you’ve got a baseline number for your potential exposure, it’s time to get it validated and build a formal plan to bring that number down. Think of your initial self-assessment as the catalyst for taking more structured, decisive action.
Your next steps should focus on making your risk management official:
- Conduct a Formal Risk Assessment: This is where you bring in the pros. A cybersecurity partner can perform a deep-dive analysis of your vulnerabilities. Their expert eyes will spot risks you might have missed and help build a far more accurate financial model of what a breach could cost you.
- Review Your Cyber Insurance Policy: If you have cyber insurance, pull out that policy and read the fine print. Sit down with your provider to review your coverage limits and exclusions. You need to make sure your policy actually covers the potential costs you’ve estimated, especially for things like regulatory fines and business interruption.
- Consult with Your IT Partner: Share what you’ve found with your managed IT or cybersecurity provider. They can help you prioritize security investments to tackle the biggest risks you’ve identified, making sure every dollar you spend on security is actually working to lower your exposure.
Data Breach Costs in Michigan: A Local View
Those big, scary global statistics on data breach costs are interesting, but they don’t really hit home. The financial gut punch of a security incident feels a lot different for a local business in Grand Rapids, a manufacturer in Detroit, or a school district up in Traverse City.
When we bring these numbers down to a local level, the threat suddenly becomes real. It highlights the specific vulnerabilities that Michigan organizations are up against every single day.
For a small or medium-sized business (SME) in our state, the fallout can be even more devastating than it is for a giant corporation. Why? Local businesses rarely have the deep cash reserves to absorb all the costs that come with a breach. A single incident can be an existential threat, which is why making proactive security a priority is non-negotiable.
Estimated Breach Cost Scenarios for Michigan SMEs
To make this tangible, we’ve put together some illustrative cost estimates. This table shows how a hypothetical data breach could play out for different types of organizations right here in Michigan, highlighting the unique factors that drive up the final bill.
| Organization Type | Estimated Record Count | Key Cost Drivers | Total Estimated Cost Range |
|---|---|---|---|
| Multi-Site Manufacturer | 1,000+ (B2B Client/Supplier Records) | Operational Downtime, Supply Chain Disruption, Expedited Shipping | $750,000 – $1.5 million |
| Healthcare Clinic (HIPAA) | 20,000 Patient Records | Regulatory Fines (HIPAA), Patient Notification, Credit Monitoring | $3 million – $5 million+ |
| Local School District | 15,000 Student & Staff Records | Notification of Minors, Credit Monitoring, Reputational Damage | $1 million – $2.2 million |
| Municipal Government | 5,000 – 10,000 Citizen Records | Public Relations, Regulatory Compliance, Loss of Public Trust | $500,000 – $1.2 million |
These figures are estimates, of course, but they paint a clear picture of the scale of financial damage a breach can inflict. The specific circumstances of each incident will always determine the final cost, but for many Michigan SMEs, these numbers would be catastrophic.
A Look at Key Michigan Industries
To really understand the impact, let’s walk through some realistic scenarios for key industries in our region. Each one faces its own set of challenges, from tough regulations to critical operational dependencies, that shape the final bill after a cyberattack.
Before diving in, it’s worth remembering that the best defense is a good offense. Implementing strong, regionally-focused cybersecurity best practices for Michigan businesses is the single most important step you can take to lower your financial risk.
- Multi-Site Manufacturing Firm: Picture a manufacturer with plants in Lansing and Flint. A ransomware attack hits, encrypting their production schedules and supplier data. The biggest cost driver here is operational downtime. Production lines grind to a halt, and supply chain chaos ensues. Just recovering the systems, paying for expedited shipping to meet deadlines, and repairing the damage to their reputation with B2B partners could easily push the total cost into the $750,000 to $1.5 million range.
- Local School District: A suburban Detroit school district discovers a hacker has stolen the personal information of 15,000 students and staff. The initial costs are for forensic investigation and notifying thousands of families. But the long-term expenses are what really add up: providing credit monitoring for minors, dealing with potential lawsuits from parents, and rebuilding the community’s trust. The final tally? An estimated $1 million to $2.2 million.
- Municipal Government: A small city government near Grand Rapids gets breached, exposing citizen data from tax and utility records. The costs here go way beyond just technical recovery. They have to manage public outrage and prove compliance with state data protection laws. The combination of regulatory heat and reputational repair could easily cost them between $500,000 and $1.2 million.
The Perfect Storm for Michigan Healthcare Providers
Healthcare organizations across Michigan are in a uniquely painful position because of the Health Insurance Portability and Accountability Act (HIPAA). For a clinic or hospital, a data breach isn’t just one problem—it’s two massive problems stacked on top of each other, creating a perfect financial storm.
First, they have to pay for all the standard recovery costs: the forensic analysis, system restoration, patient notifications, and credit monitoring. These expenses alone are a huge financial burden.
But then HIPAA enters the picture, adding a punishing layer of regulatory fines for not protecting patient data properly.
For a healthcare provider, HIPAA penalties are not just a possibility; they are a near certainty following a significant breach. These fines are calculated per violated record and can quickly escalate into the millions, often dwarfing the initial technical recovery costs.
Think about a mid-sized clinic in Ann Arbor that exposes the records of 20,000 patients. The direct and indirect costs to recover could easily hit $2 million. Then, federal regulators could swoop in and levy HIPAA fines adding another $1 million to $3 million (or more), depending on how negligent the clinic was. This one-two punch makes healthcare the most expensive industry for a data breach by a long shot—a reality felt by providers all across our state.
Common Questions About Data Breach Costs
When it comes to the financial fallout of a security incident, business leaders have a lot of the same pressing questions. Let’s cut through the noise and give you some straightforward answers, based on what we see in the field every day.
What Is the Single Biggest Factor in Data Breach Costs?
Hands down, the single biggest variable that dictates the final bill is time. More specifically, it’s the time between when an attacker gets in and when you kick them out. An incident that’s caught and contained in a few days will always, always be cheaper than one that festers for months.
Think of it like a leaky pipe in your wall. A slow drip you fix right away is a minor repair. A drip that goes unnoticed for six months leads to rotted studs, ruined drywall, and a massive mold problem. The longer an attacker has "dwell time" in your network, the more data they can steal and the deeper they can embed themselves, driving up the cost of investigation, cleanup, and recovery exponentially.
How Can a Small Business Afford to Prepare?
This is a big one. For small businesses, the key is to stop thinking about building an impenetrable fortress and start focusing on smart, high-impact strategies. You don't need an unlimited budget; you need to make shrewd, preventative investments.
Start with the essentials that give you the most bang for your buck:
Employee Training: A team that knows how to spot a phishing email is your best and most affordable first line of defense. Period.
Incident Response Plan: It costs next to nothing to sit down and document who does what during an attack. That simple piece of paper can save you an incredible amount of money and chaos when things go sideways.
Managed Cybersecurity: Partnering with a team of experts often gets you enterprise-level protection for a predictable monthly fee. It’s a far more manageable cost than the astronomical, unplanned expense of a post-breach cleanup.
Does Cyber Insurance Cover All Data Breach Costs?
No, and this is a critical point that trips up a lot of businesses. Cyber insurance is an essential financial tool, but it is not a get-out-of-jail-free card. Every policy has specific coverage limits and, just as important, a list of exclusions.
While your policy might cover direct costs like legal fees or mailing out customer notifications, it often won’t touch the indirect costs—things like the full value of your stolen intellectual property, the long-term damage to your brand’s reputation, or the cost of the security upgrades you're forced to make after the breach.
You have to read your policy carefully to understand exactly what is and isn't covered. Think of it as a financial safety net that helps you recover, not a substitute for having strong security in the first place.
Navigating the complexities of data breach prevention requires a trusted partner. Kraft Business Systems delivers the expert guidance and managed cybersecurity solutions Michigan organizations need to stay secure and resilient. Learn how we can protect your business.