Why IT Compliance Standards Are Critical for Business Success
IT compliance standards are structured sets of rules, regulations, and best practices that organizations must follow to protect sensitive data, manage cybersecurity risks, and meet legal requirements. These frameworks ensure your technology systems operate securely while adhering to industry-specific and government regulations.
Key IT Compliance Standards You Need to Know:
- GDPR – Protects EU citizen data with fines up to €20 million or 4% of global revenue
- HIPAA – Safeguards healthcare information through administrative, physical, and technical controls
- PCI DSS – Secures credit card data with 12 essential security requirements
- SOX – Ensures financial reporting accuracy and data retention for public companies
- ISO 27001 – Provides comprehensive information security management framework
- NIST CSF – Offers cybersecurity best practices through five core functions
- SOC 2 – Validates security controls for cloud and SaaS providers
The stakes for non-compliance have never been higher. According to IBM’s Cost of a Data Breach Report 2024, the global average cost of a data breach has hit an all-time high at $4.88 million, increasing by 10% from the previous year.
Beyond financial penalties, non-compliance can result in:
- Reputational damage that destroys customer trust
- Legal action and regulatory scrutiny
- Lost business opportunities and market access
- Operational disruptions from security incidents
For mid-sized businesses, understanding and implementing the right compliance standards isn’t just about avoiding penalties – it’s about building a foundation of trust with customers, partners, and stakeholders while protecting your most valuable asset: your data.
Key it compliance standards vocabulary:
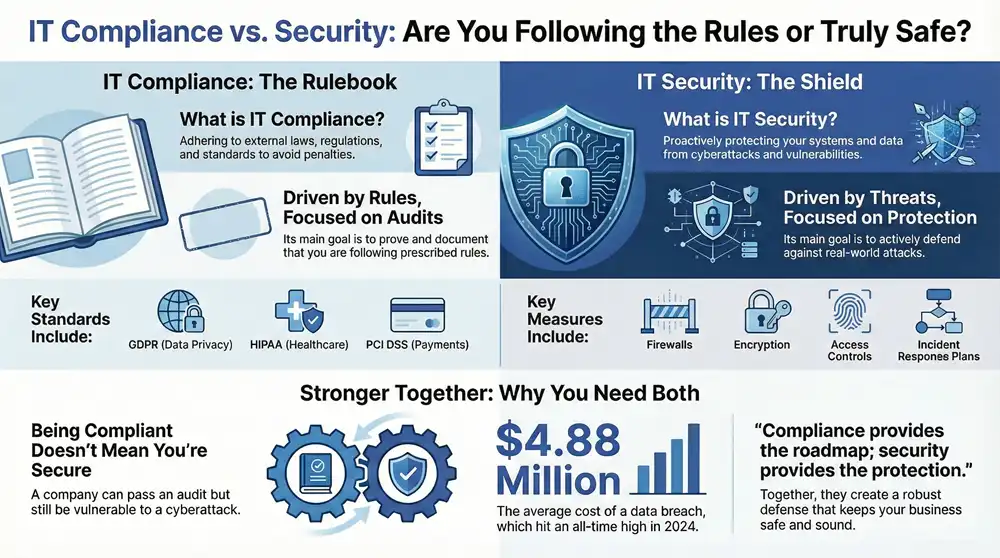
Compliance vs. Security: Understanding the Critical Difference
Picture this: you’re driving to work, following all the traffic laws while staying alert for hazards. The speed limits and stop signs represent compliance – the rules you must follow. Your defensive driving skills represent security – how you actively protect yourself from danger. Both keep you safe, but they work in completely different ways.
IT compliance is about meeting external requirements. It’s the “what” of your data protection strategy – what rules must we follow? These IT compliance standards come from government agencies, industry bodies, and regulatory organizations. They tell you exactly what you need to do to handle data legally and avoid penalties.
Think of compliance as your report card. You document your processes, undergo audits, and prove you’re following the prescribed rules. It’s often reactive – responding to regulations that already exist rather than anticipating new threats.
IT security is about active protection. It’s the “how” of keeping your systems and data safe from real-world threats. This means firewalls, encryption, access controls, and incident response plans. Security teams spend their days thinking like hackers, constantly adapting to new attack methods.
Security is proactive by nature. While compliance asks “Are we following the rules?” security asks “Are we actually safe?”
Here’s where it gets interesting: you can be compliant without being secure, and vice versa. Imagine a company that perfectly documents every required policy but runs outdated software full of security holes. They might pass their compliance audit while being completely vulnerable to cyberattacks.
On the flip side, a business might have cutting-edge security technology but fail a compliance audit because they didn’t document their processes properly or missed specific regulatory requirements.
| IT Compliance | IT Security |
|---|---|
| Focus: Meeting external rules and standards | Focus: Proactive risk mitigation and threat protection |
| Approach: Audit-focused, documentation-heavy | Approach: Technical controls, continuous monitoring |
| Driver: External mandates and regulations | Driver: Internal need to protect against cyber threats |
The magic happens when compliance and security work together. Strong security practices become the foundation for achieving compliance, while compliance frameworks provide the structured approach that ensures nothing gets overlooked.
The consequences of ignoring either side can be devastating. Failure to comply with security regulations can result in financial penalties that cripple your business, reputational damage that destroys customer trust, legal action from regulators, and lost business opportunities when partners refuse to work with non-compliant organizations.
GDPR violations alone can cost up to 4% of your global annual revenue – a penalty that has forced some companies out of business entirely. But the hidden costs often hurt more: customers who stop trusting you with their data, contracts you can’t win because you lack proper certifications, and the operational chaos that follows a major security incident.
The bottom line? You need both compliance and security working hand in hand. One provides the roadmap, the other provides the protection. Together, they create a robust defense that keeps your business safe and legally sound.
For more insights on how these critical areas work together, check out our guide on IT Compliance and Security.
A Guide to the Most Critical IT Compliance Standards
Navigating IT compliance standards can feel overwhelming – like trying to read a map written in a dozen different languages. The good news? You don’t need to master every single framework out there. What matters is understanding which ones apply to your business and why they exist in the first place.
Think of compliance standards as different safety nets, each designed to catch specific types of risks. Some are mandatory based on your industry or location, while others are voluntary frameworks that can strengthen your overall security posture. Let’s break down the most critical ones you need to know about.
For Data Privacy: GDPR & CCPA
Data privacy regulations have become the global standard for protecting personal information, and they pack a serious punch when it comes to enforcement.
The General Data Protection Regulation (GDPR) is Europe’s game-changing privacy law that applies to any organization handling EU citizens’ personal data – regardless of where your business is located. If you have customers, employees, or even website visitors from Europe, GDPR likely applies to you. The GDPR is a European Union data privacy law that revolves around core principles like obtaining explicit consent, collecting only what you need, and respecting data subject rights.
These rights include the ability for individuals to access their data, correct it, delete it, or take it with them to another service. The financial stakes are enormous – fines can reach up to 4% of global revenue or €20 million, whichever is higher. That’s not pocket change for any business.
The California Consumer Privacy Act (CCPA) serves as America’s answer to GDPR, giving California residents significant control over their personal information. What makes CCPA particularly interesting is its broader definition of personal data, which includes any information that can be used to create inferences about a person’s preferences or behavior. California residents can opt-out of data sales, know what information is collected about them, and request deletion of their data.
For Healthcare: HIPAA
Healthcare organizations face unique challenges when it comes to protecting sensitive patient information. The Health Insurance Portability and Accountability Act (HIPAA) sets the standard for safeguarding Protected Health Information (PHI) and its electronic counterpart (ePHI).
The HIPAA Security Rule requires three types of safeguards that work together like layers of protection. Administrative safeguards include security management processes and workforce training. Physical safeguards control facility access and workstation security. Technical safeguards involve encryption, access controls, and audit logs.
The consequences of HIPAA violations can be devastating. When Anthem faced a data breach affecting nearly 79 million people, they paid $16 million in fines. For healthcare providers, HIPAA compliance isn’t just about avoiding penalties – it’s about maintaining the sacred trust patients place in their care providers.
If you’re in healthcare, our Healthcare IT Compliance Services can help you steer these critical requirements with confidence.
For Finance & Payments: PCI DSS & SOX
Money matters require special attention, and the financial sector has developed some of the most rigorous compliance standards in existence.
The Payment Card Industry Data Security Standard (PCI DSS) protects cardholder data through The PCI DSS 12 requirements. Here’s the interesting twist: PCI DSS isn’t actually a law – it’s an industry standard enforced by credit card companies. But don’t let that fool you into thinking it’s optional. Non-compliance can result in hefty fines, increased transaction fees, or even losing your ability to process credit cards altogether.
The 12 requirements cover everything from building secure networks with firewalls to protecting stored cardholder data, maintaining vulnerability management programs, implementing strong access controls, regularly monitoring networks, and maintaining comprehensive information security policies.
The Sarbanes-Oxley Act (SOX) emerged from major corporate scandals and focuses on financial reporting integrity. While it might seem like a finance-only concern, IT plays a crucial role in SOX compliance. Your technology systems must ensure data retention policies are followed, access to financial systems is properly controlled, and audit trails are maintained for all financial data.
For Information Security Management: ISO 27001 & NIST
Some organizations want a comprehensive approach to information security that goes beyond specific regulatory requirements.
ISO/IEC 27001 provides an internationally recognized framework for Information Security Management Systems (ISMS). It takes a risk-based approach where you identify your specific security risks and implement appropriate controls to manage them. While voluntary, ISO 27001 certification demonstrates a serious commitment to information security that can open doors with security-conscious clients and partners.
The National Institute of Standards and Technology (NIST) offers The NIST Cybersecurity Framework (CSF), which has become the gold standard for cybersecurity best practices. The framework is built around five core functions that create a comprehensive security strategy: Identify your assets and risks, Protect your critical services, Detect cybersecurity events, Respond to incidents, and Recover from attacks.
What makes NIST particularly valuable is its practical approach. Rather than prescribing specific technologies, it provides a flexible framework that works for organizations of any size or industry.
For Cloud & Service Providers: SOC 2
In our cloud-first world, service providers need a way to prove they’re handling customer data responsibly.
Service Organization Control 2 (SOC 2) was developed by the American Institute of Certified Public Accountants (AICPA) specifically for technology and cloud service companies. The SOC 2 framework evaluates service providers based on five Trust Services Criteria.
Security ensures protection against unauthorized access and system damage. Availability guarantees systems are accessible when needed. Processing Integrity verifies that system processing is complete, accurate, and authorized. Confidentiality protects sensitive information according to agreements. Privacy ensures personal information is handled according to privacy notices and best practices.
For SaaS companies and cloud vendors, SOC 2 compliance has become essential for building customer trust. It’s often a requirement in enterprise sales processes, as clients want assurance that their data is protected according to rigorous, independently verified standards.
Understanding which IT compliance standards apply to your business is the first step toward building a robust compliance program. The key is starting with what’s mandatory for your industry and location, then building outward with frameworks that strengthen your overall security posture.
Building Your IT Compliance Framework: A Step-by-Step Approach
Creating an effective it compliance standards program might feel overwhelming at first, but it doesn’t have to be. Think of it like building a house – you need a solid foundation, the right materials, and a clear plan. The good news? You don’t have to figure it all out alone. As your partners serving businesses from Grand Rapids to Detroit, and everywhere in between including Ann Arbor and Traverse City, we’ve helped countless organizations steer this journey successfully.
The key is understanding that compliance isn’t a destination – it’s an ongoing process that evolves with your business. Let’s break down how to build a framework that actually works for your organization.
How to Choose the Right IT Compliance Standards for Your Business
Here’s the truth: not every compliance standard applies to every business. Trying to implement everything at once is like trying to eat an entire pizza in one bite – it’s messy, ineffective, and you’ll probably choke.
Start by taking a step back and looking at your business through a compliance lens. Industry requirements are usually your first clue. If you’re in healthcare, HIPAA isn’t optional – it’s the law. Running an e-commerce site? PCI DSS becomes your best friend the moment you process that first credit card payment. Government contractors need to think about NIST frameworks right from the start.
Geographic scope matters more than you might think. Serving customers in California means CCPA is on your radar, even if your business is headquartered in Michigan. Have European customers visiting your website? Congratulations, you’re now in GDPR territory. It’s not just about where you are – it’s about where your data goes.
The types of data you handle tell an important story too. Personal information, health records, financial data, and intellectual property each come with their own set of rules. A manufacturing company handling employee records faces different requirements than a SaaS provider storing customer analytics.
Don’t forget about customer expectations. Your biggest client might require SOC 2 reports before they’ll even consider renewing their contract. These business-driven requirements are just as important as legal mandates.
Before diving headfirst into any framework, conduct a risk assessment to understand your current security posture and identify gaps. This isn’t just paperwork – it’s your roadmap for prioritizing efforts and resources. Our IT Compliance Risk Assessment guide can help you get started on the right foot.
Once you’ve mapped out your requirements, prioritize frameworks strategically. Handle mandatory regulations first – you can’t negotiate with the law. Then consider foundational frameworks like NIST CSF or ISO 27001, which provide excellent security practices that often support multiple compliance goals simultaneously.
Key Components of a Robust Compliance Program
Building a compliance program that actually works requires more than just checking boxes on an audit form. It’s about creating a culture where security and compliance become natural parts of how your team operates.
Risk management forms the foundation of everything else you’ll build. This isn’t a one-time assessment you file away and forget. It’s an ongoing process of identifying threats, understanding vulnerabilities, and measuring potential impact. Think of it as your early warning system – the better you understand your risks, the better you can protect against them.
Policy and procedure development might sound boring, but these documents are your compliance lifeline. They need to be clear enough that a new employee can understand them, comprehensive enough to cover real-world scenarios, and updated regularly as your business evolves. Nobody wants to read a 200-page policy manual, so keep them practical and actionable.
Access controls ensure that the right people have access to the right information at the right time – and everyone else doesn’t. This means implementing multi-factor authentication, role-based access controls, and regular access reviews. It’s amazing how often former employees still have access to systems months after they’ve left.
Security awareness training turns your employees from potential security risks into your first line of defense. But here’s the thing – boring, annual training sessions don’t work. Make it engaging, relevant to their daily work, and regular enough that security thinking becomes second nature.
Continuous monitoring keeps your finger on the pulse of your compliance posture. Instead of finding problems during your annual audit, you catch and fix issues as they happen. It’s the difference between a smoke detector and a fire department – both are important, but one prevents disasters.
Incident response planning acknowledges a simple truth: despite your best efforts, things can go wrong. A well-tested incident response plan helps you contain damage, recover quickly, and meet regulatory reporting requirements. The key word here is “tested” – a plan that’s never been practiced is just expensive paperwork.
Regular audits and reviews provide external validation that your controls are working as intended. They also help identify blind spots and areas for improvement. For detailed guidance on preparing for and managing audits, check out our IT Compliance Audit Guide.
The Role of Technology and Automation
Let’s be honest – managing compliance manually is like trying to count grains of sand on a beach. It’s technically possible, but there are much better ways to spend your time.
Governance, Risk, and Compliance (GRC) platforms act as your command center, bringing all your compliance activities under one roof. Instead of juggling spreadsheets, email chains, and sticky notes, you get a centralized view of your entire compliance posture. These platforms help streamline risk assessments, manage policies, track control implementation, and prepare for audits.
Automated evidence collection eliminates one of the most tedious aspects of compliance – gathering proof that your controls are working. Instead of scrambling to collect system logs, access reports, and configuration screenshots when audit time rolls around, automation tools continuously gather and organize this evidence. Your audit preparation time drops from weeks to days.
Continuous Controls Monitoring (CCM) provides real-time visibility into your compliance status. Rather than finding policy violations during quarterly reviews, you get immediate alerts when something goes sideways. It’s like having a security guard who never sleeps, never gets distracted, and never misses anything important.
Security Information and Event Management (SIEM) systems aggregate and analyze security data from across your entire IT infrastructure. This enables real-time threat detection and response, which is crucial for meeting regulations that require timely incident reporting. Plus, SIEM systems provide the detailed logs and forensic capabilities that auditors love to see.
The beauty of leveraging these technologies is that they reduce manual effort, improve accuracy, and free up your IT team to focus on strategic initiatives rather than compliance paperwork. We’re talking about making compliance an integrated part of your operations, not a quarterly scramble to get ready for audits.
To explore how these tools can transform your compliance program, take a look at our insights on GRC Compliance Tools. The right technology stack can make the difference between compliance being a burden and compliance being a competitive advantage.
Frequently Asked Questions about IT Compliance Standards
When we’re working with businesses across Michigan – from Grand Rapids to Ann Arbor – we hear the same questions about it compliance standards over and over again. These concerns are completely understandable; compliance can feel overwhelming when you’re trying to run a business and keep your customers happy. Let’s tackle the most common questions we encounter.
What is the difference between IT compliance and IT security?
This is probably the question we get asked most often, and it's a great one because understanding this distinction is crucial for making smart decisions about your technology investments.
IT compliance is essentially about following the rules - it's the act of adhering to external laws, regulations, and industry standards that apply to your business. Think of it like following building codes when constructing an office. You need to meet specific requirements, document that you're meeting them, and often prove it through audits. Compliance is reactive by nature; it responds to what regulators and industry bodies say you must do.
IT security, on the other hand, is your active defense system. It's the broader practice of implementing technical and procedural controls to proactively protect your systems and data from real-world threats like cyberattacks, malware, and unauthorized access. If compliance is following the building codes, security is installing the best locks, alarm systems, and security cameras you can afford.
Here's where it gets interesting: you can be compliant without being fully secure. Imagine a business that checks every compliance box perfectly but uses outdated, easily hackable software. They might sail through an audit but still get breached by cybercriminals. Conversely, you could have excellent technical security but fail a compliance audit because you didn't document your processes correctly.
The sweet spot is where both work together. A strong security posture provides the foundation for maintaining robust compliance over time, while compliance frameworks give you structured guidelines for implementing security controls systematically.
Which IT compliance standard is the most important?
We wish we could give you a simple answer here, but the truth is there's no single "most important" standard. It's like asking which tool is most important in a toolbox - it depends entirely on what job you're trying to do.
Your industry dictates much of this decision. For healthcare organizations handling patient data, HIPAA is absolutely critical - there's no way around it. If you're running an e-commerce business or processing credit card payments in any capacity, PCI DSS becomes non-negotiable. Companies dealing with data from EU citizens must comply with GDPR, regardless of where their business is physically located.
For businesses without specific industry mandates, many organizations start with foundational frameworks like NIST CSF or ISO 27001. These provide comprehensive security best practices that create a solid baseline for future compliance efforts. They're like building a strong foundation that makes it easier to add specific compliance requirements later.
The right standard for your business is the one that applies directly to your operations, your customers, and the types of data you handle. When we work with new clients, we always start by mapping out their specific compliance landscape before recommending any particular framework.
What are the first steps to becoming IT compliant?
Getting started with compliance doesn't have to feel like climbing Mount Everest. We've helped dozens of Michigan businesses through this process, and there's a logical path that makes it much more manageable.
Start with a comprehensive assessment of your current situation. This means identifying which specific laws, regulations, and industry standards actually apply to your business. Consider your industry, where your customers are located, what types of data you collect and store, and what your clients or partners might require from you. This isn't guesswork - it's detective work that requires looking at your business through a regulatory lens.
Once you know what applies to you, conduct a thorough gap analysis. This is where you compare your current IT practices and security controls against the requirements of the identified standards. Be honest about where you stand - this isn't about judgment, it's about creating an accurate roadmap. You might find you're closer to compliance than you thought, or you might uncover areas that need immediate attention.
Develop a strategic roadmap based on your gap analysis. This should prioritize the most critical gaps first - usually those that pose the highest risk or are required by mandatory regulations. Your roadmap should include implementing necessary policies, upgrading technical controls, and establishing employee training programs.
For a deeper dive into this assessment process, check out our detailed guide on IT Compliance Risk Assessment. This is a journey that benefits tremendously from expert guidance - you don't have to figure it all out alone.
The key is starting with small, manageable steps rather than trying to tackle everything at once. We've seen businesses get overwhelmed trying to implement five different compliance frameworks simultaneously. Focus on the most critical requirements first, build momentum, and expand from there.
Conclusion
As we wrap up our journey through it compliance standards, this isn’t a destination you reach and then forget about. IT compliance is a continuous journey that evolves alongside new threats, technological breakthroughs, and changing regulatory landscapes. Think of it like maintaining your health – you can’t just eat well for a month and expect to stay fit forever.
The stakes are real, and they’re growing every year. We’ve seen how the average data breach now costs nearly $5 million, and that’s just the financial impact. The damage to your reputation and customer trust can be far more devastating and much harder to repair. But here’s the thing – when you get compliance right, it becomes so much more than just avoiding penalties.
Robust adherence to it compliance standards transforms your business in powerful ways. It protects the sensitive data your customers trust you with, builds unshakeable confidence in your brand, and ensures your operations can weather the storms that inevitably come. When prospects see that you take data protection seriously, it becomes a competitive advantage that sets you apart.
We know navigating this complex web of regulations can feel overwhelming. Between GDPR’s privacy requirements, HIPAA’s healthcare protections, PCI DSS’s payment security standards, and all the other frameworks we’ve discussed, it’s easy to feel lost in acronyms and requirements. That’s completely normal, and you’re not alone in feeling that way.
At Kraft Business Systems, we’ve been helping businesses across Michigan – from the busy streets of Grand Rapids to the quiet shores of Glen Arbor – turn compliance challenges into strategic advantages. We understand that every business is unique, with its own specific needs and constraints. That’s why we don’t believe in one-size-fits-all solutions.
Instead, we work alongside you to build a compliance program that makes sense for your organization, your industry, and your goals. We help transform what often feels like a burden into a foundation for growth and customer confidence. Because when compliance is done right, it’s not just about checking boxes – it’s about building a business that customers can trust completely.
Ready to take the next step in your compliance journey? Explore our comprehensive IT Solutions and find how we can help you build a robust, sustainable compliance program that protects your business and empowers your growth.