IT compliance can feel like a dense, technical subject, but at its core, it’s all about one thing: making sure your technology and data practices follow the rules. These rules, set by legal, regulatory, and industry bodies, are there for a reason—to protect sensitive information, build trust with your customers, and help you dodge the massive fines that come with getting it wrong. This isn’t just an IT problem; it’s a fundamental part of business integrity.
What Are IT Compliance Services
Think of IT compliance services as the mandatory safety inspections and regular maintenance for your company’s “digital engine.” Just like a commercial truck has to pass specific checks to be road-legal and safe, your company’s entire IT setup—from servers to employee laptops—has to meet strict standards for handling data securely.
These services go way beyond a simple “check-the-box” exercise. They’re a core business function designed to guard your most valuable assets: your data and your reputation. For a small or mid-sized business in Michigan, falling short on these standards can lead to penalties that sting much more than just fines. We’re talking about losing customer trust and facing operational shutdowns that could cripple your business.
The Core Pillars of Compliance Management
At its heart, managing compliance is all about proactive risk management. It’s about knowing which rules apply to you and having a systematic plan to follow them. Professional it compliance services break this down into three essential pillars:
- Assessment: This is the diagnostic phase. Experts dig into your current systems, policies, and procedures to find any gaps between what you’re doing and what the regulations demand.
- Remediation: Once the problems are spotted, it’s time to fix them. This could mean anything from installing new security tools and rewriting internal policies to training your team on how to handle data safely.
- Monitoring: Compliance isn’t a one-and-done project. Continuous monitoring uses specialized tools and regular check-ins to make sure your defenses stay strong and new weak spots are fixed before they become big problems.
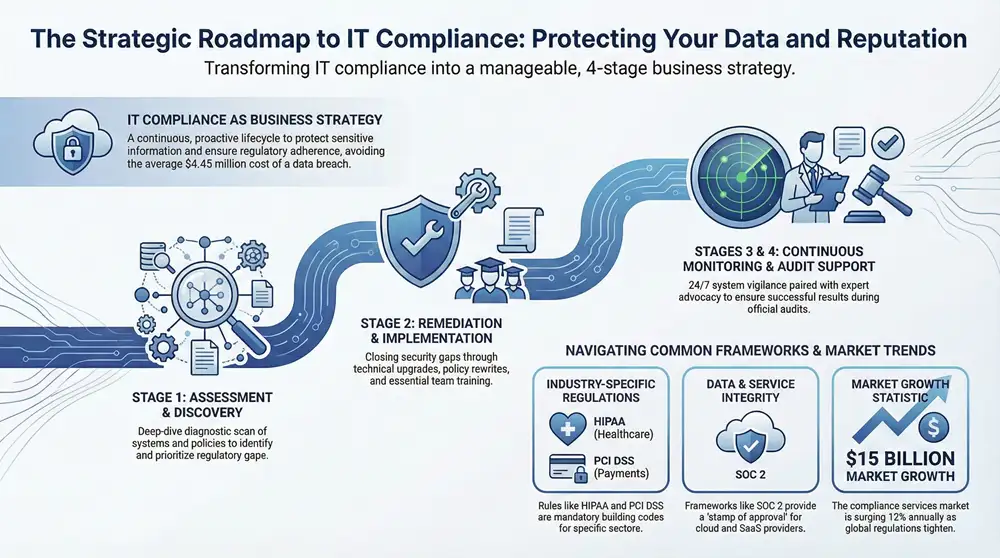
This structured approach takes what can feel like an overwhelming technical burden and turns it into a manageable, essential business strategy. It gives you a clear roadmap to protect your company from both regulatory heat and cyber threats.
An effective compliance strategy is a powerful business enabler. It signals to customers, partners, and regulators that you take data protection seriously, creating a foundation of trust that can become a significant competitive advantage.
From Technical Task to Business Strategy
Viewing compliance as just another technical chore is a huge mistake. A well-run program delivers real business benefits that go far beyond just avoiding fines. For one, it strengthens your overall security, making you tougher against data breaches that now cost an average of $4.45 million per incident.
This proactive approach to security and rules is a key differentiator in the market. You can learn more about how these concepts connect in our detailed guide on IT compliance and governance. It’s also helpful to see what tools are out there. To get a better feel for what these services can do, take a look at these Top Compliance Management Solutions. Ultimately, investing in compliance is an investment in your company’s stability, reputation, and long-term success.
Decoding Common Compliance Frameworks
Trying to get a handle on compliance frameworks can feel like you’re drowning in alphabet soup. You hear acronyms like HIPAA, PCI DSS, and SOC 2 thrown around constantly, but each one is a unique set of rules built for a very specific job.
Think of them like different building codes. You wouldn’t use the specs for a downtown Detroit skyscraper to build a house in Traverse City, right? In the same way, you wouldn’t apply the data security rules for a hospital to a local coffee shop. Each framework gives you a structured blueprint for protecting certain kinds of information. It’s not about trying to follow every rule under the sun; it’s about mastering the ones that apply directly to your business.
Frameworks Tied to Industry
Many of the most common regulations are directly linked to the industry you’re in. These rules exist because some sectors handle incredibly sensitive data, and a breach could cause serious, real-world harm to people.
For instance, any healthcare organization in Michigan, from a small doctor’s office to a major hospital system, has to live and breathe the Health Insurance Portability and Accountability Act (HIPAA). Its whole purpose is to protect patient health information (PHI). That means having iron-clad controls over who can access medical records and making sure that data is encrypted, whether it’s just sitting on a server or being sent over the network.
In the same vein, any business that takes credit card payments—online or in a physical store—is subject to the Payment Card Industry Data Security Standard (PCI DSS). This framework is laser-focused on one thing: securing credit card data to stop fraud in its tracks. A core part of PCI DSS is maintaining a secure network and constantly testing your security systems to find weak spots before the bad guys do.
The need for these structured rules is fueling massive growth. The global IT compliance services market is expected to hit $15 billion by 2025 and is growing at a healthy 12% each year through 2033 as regulations get even tighter.
Frameworks Focused on Data and Service Integrity
Beyond the industry-specific rules, other frameworks concentrate on how trustworthy a company’s services are and how well it handles its clients’ data. These are especially critical for tech companies and service providers that other businesses depend on to function.
A perfect example is SOC 2 (Service Organization Control 2). This framework is designed for any company that stores or processes customer data in the cloud, like a SaaS provider or a managed IT firm. A SOC 2 report is essentially a stamp of approval, showing that a company has solid controls in place for security, availability, processing integrity, confidentiality, and privacy.
Getting compliant often means building a complete governance, risk, and compliance framework that ties all these pieces together. It’s also vital to manage the entire lifecycle of your data. For example, when you get rid of old equipment, understanding hard drive destruction certificates is key to proving you’ve met regulatory requirements and protected that data to the very end.
Key IT Compliance Frameworks at a Glance
To help you get a clearer picture of which of these frameworks might be on your radar, here’s a quick comparison of the big ones.
| Framework | Primary Focus | Applicable Industries | Example Requirement |
|---|---|---|---|
| HIPAA | Protecting patient health information (PHI) | Healthcare providers, insurers, and their business associates | Implementing access controls to ensure only authorized personnel can view patient records. |
| PCI DSS | Securing credit card and cardholder data | Retail, e-commerce, hospitality—any business processing card payments | Encrypting all transmissions of cardholder data across open, public networks. |
| SOC 2 | Ensuring security and availability of a service provider’s systems | SaaS companies, cloud providers, data centers, managed service providers | Establishing and testing a formal incident response plan to handle security breaches. |
| GDPR | Protecting the personal data and privacy of EU citizens | Any organization worldwide that processes the data of EU residents | Obtaining explicit consent from individuals before collecting and processing their data. |
Ultimately, choosing the right it compliance services partner means finding someone who doesn’t just know these frameworks inside and out, but who understands how to apply them to your specific business—making sure you meet your obligations without adding unnecessary cost or complexity.
The Four Stages of an Effective Compliance Program
Getting your IT compliance in order isn’t a one-and-done project. It’s a continuous journey, a structured lifecycle that turns the vague idea of “being compliant” into a manageable, ongoing program. Each stage builds on the one before it, creating a tough, resilient framework that protects your company’s data and, just as importantly, its reputation.
This process has to adapt to different industries, whether you’re handling patient data in healthcare, financial records, or tech-specific regulations.
While the core steps—assess, fix, monitor, prove—stay the same, the specific rules and security controls are tailored to the unique risks each sector faces.
Stage 1: Assessment and Discovery
The journey always kicks off with a thorough assessment. Think of this as a diagnostic scan for your entire technology environment. A compliance expert plays detective, meticulously digging into your current systems, policies, and procedures to see how they stack up against the standards you’re required to meet.
This first phase is absolutely critical because it creates the roadmap for everything that follows. It’s not just about finding flaws; it’s about understanding why they exist in the first place. You’ll walk away with a detailed report that pinpoints specific gaps, prioritizes risks, and lays out a clear plan of attack.
Stage 2: Remediation and Implementation
With that roadmap in hand, it’s time for remediation. This is the hands-on treatment phase where you start closing the gaps you found during the assessment. It’s where policies get written, security controls are put in place, and your team gets the training they need to maintain the new standards.
This can involve a whole range of activities, from deploying new security software to reconfiguring network settings. For a Michigan healthcare clinic, this might mean implementing stronger encryption for patient data to satisfy HIPAA. For a local retailer, it could mean locking down their payment systems to align with PCI DSS.
The goal here is tangible improvement. You’re taking the theoretical findings from the assessment and turning them into real-world security and operational upgrades.
Stage 3: Continuous Monitoring
Compliance isn’t a finish line you cross once; it’s a state you have to maintain. The third stage, continuous monitoring, is like an ongoing wellness plan for your IT systems. It involves using automated tools and regular check-ups to make sure your defenses stay strong and effective.
Continuous monitoring transforms compliance from a reactive, stressful event into a proactive, manageable business function. It provides the peace of mind that comes from knowing you are always prepared for an audit and protected against emerging threats.
This constant vigilance is essential. New threats pop up all the time, and your business operations change, creating potential new weak spots. Monitoring services keep an eye on your systems 24/7, flagging suspicious activity and confirming that your controls are working as intended. This keeps small issues from snowballing into major compliance failures.
Interestingly, there’s a shift happening in the market. While managed services hold a significant 19% share, the advisory-led model is catching fire, with a projected surge of nearly 30% from 2024 to 2025 as providers blend consulting with delivery. You can dive deeper into this evolving service model in Apptega’s 2025 report.
Stage 4: Audit Support and Reporting
The final stage is audit support. When an official auditor comes knocking, this is where your IT compliance services provider becomes your expert advocate. Having a pro in your corner can be the difference between a smooth process and a stressful, resource-draining nightmare.
Your provider helps you get ready by organizing all the necessary documents, running pre-audit checks, and making sure your team knows what to expect. During the audit itself, they act as a translator, answering technical questions and demonstrating that all the required controls are in place and working correctly. This expert guidance helps you navigate the whole ordeal with confidence and come out with a successful result.
Why Outsourcing IT Compliance Is a Smart Business Move
For a lot of businesses, the idea of handling IT compliance in-house feels like the practical, cost-saving route. But this DIY approach is often a false economy. It hides deep, complex expenses that go way beyond just one employee’s salary. Partnering with a specialist turns a reactive headache into a predictable, strategic advantage.
Building an internal compliance team is a serious financial commitment. It starts with hiring experts who command high salaries, and it doesn’t stop there. You have to continuously invest in their training to keep up with constantly changing regulations. On top of that, you need to buy and maintain expensive security and monitoring tools that are often out of reach for a single small or mid-sized company.
When you outsource, you get immediate access to a team of seasoned pros and their entire tech stack for a predictable, scalable fee. It completely changes the financial equation.
The True Cost of an In-House Team
The sticker shock of hiring a dedicated compliance officer is just the tip of the iceberg. The hidden costs pile up fast, creating a massive and often unpredictable drain on your resources. A truly effective in-house program needs more than one person; it demands a team with a diverse range of skills.
Think about all the expenses that come with it:
- Specialist Salaries: Certified compliance and cybersecurity professionals are in high demand, and their paychecks reflect that scarcity.
- Ongoing Education: Regulations like HIPAA and PCI DSS are always being updated. Your team will need constant training, certifications, and conference tickets to stay current, all of which come with hefty price tags.
- Advanced Technology: Enterprise-grade tools like SIEM (Security Information and Event Management) systems, vulnerability scanners, and monitoring platforms are non-negotiable for modern compliance. These tools come with steep licensing fees, implementation costs, and ongoing maintenance.
Outsourcing IT compliance services lets you tap into a shared pool of world-class expertise and technology at a fraction of what it would cost to build it yourself. It converts a large, unpredictable capital expense into a stable, predictable operational one.
Free Your Team to Focus on Growth
Maybe the biggest win from outsourcing is strategic focus. Every single hour your internal IT team spends trying to decipher complex regulations, prep for an audit, or manage compliance tools is an hour they aren’t spending on projects that actually make you money. These tasks are critical, but they don’t directly contribute to innovation, better customer service, or growing the business.
By handing off these specialized duties, you liberate your most valuable technical talent. They can now get back to what they do best: improving business processes, developing new products, and supporting the core mission of your organization. Partnering up for managed compliance services ensures this critical function is handled by dedicated experts, giving you and your team peace of mind and the freedom to innovate.
Let’s be honest, organizations simply cannot afford to ignore these rules. With global data breaches now costing an average of $4.45 million per incident, the stakes are sky-high. Reflecting this urgency, U.S. federal agencies earmarked $13 billion for new IT contracts in just the first half of 2024, with compliance woven into every investment. You can see more in this IT compliance market report.
This shift in thinking turns compliance from a defensive chore into a proactive business enabler. It becomes a powerful competitive advantage, showing clients and partners that you are a secure and trustworthy steward of their data. Ultimately, that strengthens your brand and supports long-term success.
Breaking Down the Costs of Compliance Services
Let’s talk about the money side of things. When you start looking into IT compliance services, one of the first questions is always, “What’s this going to cost me?” It’s a critical question for any business leader, and the answer isn’t a simple, flat number you can pull off a shelf.
The price tag is flexible, scaling up or down based on exactly what your business needs. Before we get into the numbers, though, it’s important to shift your mindset. Stop thinking of compliance as a pure expense. It’s really an investment in risk management. The money you spend upfront on a solid compliance program is just a fraction of what you’d face after a data breach or a hefty regulatory fine—costs that can easily skyrocket into the millions.
Common Pricing Models Explained
Most providers offering IT compliance services use one of a few standard pricing structures. The right one for you usually depends on whether you need a one-off project or a long-term partner to keep you on track.
- Project-Based Fees: This is perfect for specific, clearly defined tasks. Think of an initial risk assessment or a gap analysis to see how you stack up against a regulation like HIPAA. You pay a fixed price for a concrete result.
- Monthly Retainer: For ongoing compliance management, a monthly retainer is the way to go. This typically covers continuous monitoring, regular reports, policy updates, and having an expert on call. It gives you predictable spending you can budget for.
- Time and Materials: You’ll see this model pop up for more specialized work, like consulting on a unique problem or helping with an emergency incident response. It’s less common for a full managed compliance program but useful for unpredictable needs.
Key Factors That Influence Your Investment
No two compliance programs are identical, and the final price will reflect the complexity of your business. Several key things will directly move the needle on your total investment.
The goal isn’t to find the cheapest option, but the one that delivers the most value by effectively minimizing your specific risks. A low-cost service that misses a critical regulatory requirement is no bargain at all.
Thinking about these factors ahead of time will help you get a better feel for what to expect and lead to a much more productive chat with potential providers.
Your Business Profile and Regulatory Burden
The biggest cost drivers are tied directly to how you operate and what industry you’re in. A small, Michigan-based retailer that just needs PCI DSS compliance will have a completely different cost structure than a healthcare provider with multiple locations juggling HIPAA, HITECH, and other state privacy laws.
Here are the main variables we look at:
- Company Size: The number of employees, computers, and physical locations all play a role. More endpoints and people mean a larger surface area to assess, secure, and monitor.
- IT Complexity: A business with a simple, on-premise server is a lot easier to manage than one with a hybrid-cloud environment, dozens of SaaS apps, and a remote workforce scattered everywhere.
- Regulatory Scope: This is a big one. The number and strictness of the frameworks you have to follow are major factors. A company that needs both SOC 2 and GDPR compliance is facing a much more involved and costly process than one just focused on a single standard.
Ultimately, the cost of IT compliance services is a strategic investment in your company’s resilience. It’s what protects you from crippling fines, keeps your customers’ trust, and builds a secure foundation so you can actually focus on growing your business.
How to Choose the Right IT Compliance Partner
Picking a partner for your IT compliance services is one of the most important decisions you’ll make. This goes way beyond just comparing prices on a spreadsheet. You’re handing over the keys to your most sensitive data and, in many ways, your company’s reputation.
The right partner becomes an extension of your own team. They take the dense, confusing language of regulations and turn it into a practical security plan that actually works for your business. A mismatch here isn’t just inefficient; it can lead to gaping security holes, failed audits, and a world of headaches.
Evaluating Expertise and Industry Fit
Your first filter should be industry experience. It’s non-negotiable. A firm that’s brilliant with manufacturing clients in Grand Rapids might not grasp the deep nuances of HIPAA needed to serve a healthcare clinic in Traverse City. You need to see a proven track record of guiding businesses just like yours through the exact same frameworks you’re facing.
Ask them for case studies or, even better, references from companies of a similar size and in the same line of work. This is the only way to verify their claims and feel confident they’ve already tackled the kinds of problems you’re about to run into.
Key Questions to Ask Potential Providers
You need to walk into these conversations ready to ask tough, specific questions. Their answers (or lack thereof) will tell you everything you need to know about their expertise, how they operate, and whether they truly care about their clients’ success. Vague, hand-wavy responses are a massive red flag.
Here’s a checklist of questions to get you started:
- How do you keep up with constantly changing regulations?
Compliance is always a moving target. A good provider will have a clear, documented process for tracking changes and proactively updating your strategy—not just reacting after the fact. - Walk me through your documented process for a security incident.
They must have a well-rehearsed incident response plan. Don’t let them off with a generic answer. Ask them to describe the literal steps they would take if your business got hit with a data breach tomorrow. - What does your communication and reporting look like?
You need total transparency. Find out how often you’ll get reports, what metrics they track, and who your dedicated point of contact will be for both daily questions and bigger strategic talks. - What specific tools and technologies do you use for monitoring?
You don’t need to be a tech genius, but getting a sense of their tech stack gives you insight into how sophisticated their operation is. It shows you whether they are investing in the right tools to protect you.
A great partner does more than just check boxes; they provide strategic guidance that aligns your compliance program with your broader business goals. They should be able to clearly articulate how their services reduce risk, build customer trust, and support your company’s growth.
Finding the right fit means looking for a provider who is as invested in your business’s security and success as you are. Their ability to give you clear, confident answers will show you if they have the expertise and process-driven approach needed to protect your organization. A true partner makes compliance feel less like a burden and more like a competitive advantage.
Frequently Asked Questions About IT Compliance
When you start digging into IT compliance, a few common-sense questions always pop up. Getting straight answers to these initial hurdles can make the whole process feel a lot less intimidating and show you where an expert can really make a difference. Let’s tackle the questions we hear most often from Michigan business owners.
What Is the First Step in Becoming IT Compliant?
Everything starts with a thorough risk assessment. Think of it like a comprehensive physical for your business's technology. A compliance expert will come in and evaluate everything—your current IT setup, your internal policies, how your team actually works day-to-day—to find the specific gaps between what you're doing and what regulations require.
This isn't just a simple check-up; it produces a detailed, actionable roadmap that guides every single thing we do next, from fixing issues to setting up ongoing monitoring.
How Long Does It Take to Achieve Compliance?
Honestly, there's no magic number here. The timeline depends entirely on your company's size, the complexity of your systems, and which specific rulebooks you need to follow. A small local business might get the essentials locked down in a few months. A larger organization with multiple offices could easily spend over a year putting all the right controls in place.
The most important thing to remember is that compliance isn't a one-and-done project with a finish line. It’s a continuous, ongoing process of improvement and vigilance. Your security needs and the regulations themselves will change, and your compliance program has to keep up.
Can I Use Software to Manage Compliance Myself?
While there's some great compliance management software out there, it's a tool, not a replacement for expertise. Think of it this way: a calculator is great for doing math, but it can't tell you how to run your business finances.
Software is fantastic for automating scans, flagging technical issues, and tracking your progress. But it can’t provide the strategic guidance, create custom policies that fit your unique business, or do the hands-on work to fix the problems it finds. For most businesses, the winning formula is a combination of an expert service partner backed by the right technology. That way, you get both strategic oversight and efficient execution.
Ready to turn your compliance obligations into a strategic advantage? Kraft Business Systems delivers expert guidance and managed services to help Michigan businesses navigate complex regulations with confidence. Secure your operations and protect your reputation today.